
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
5 Phishing Statistics Every Business Should Know
GetApp's data security survey found that most companies are still vulnerable to phishing schemes and the vast majority don't provide enough training to prevent them.

Phishing is almost as old as the internet itself, yet it's still one of the most effective methods cybercriminals use to install malware and steal sensitive data. Phishing techniques endure because they exploit people rather than technology. That means security awareness is key to staving off phishing attacks that commonly result in data breaches and serious cyber attacks.
Unfortunately, GetApp's data security survey found that most companies remain vulnerable to phishing schemes and do not put enough emphasis on data security training. In this article, we'll take a closer look at the phishing statistics we pulled from our findings.
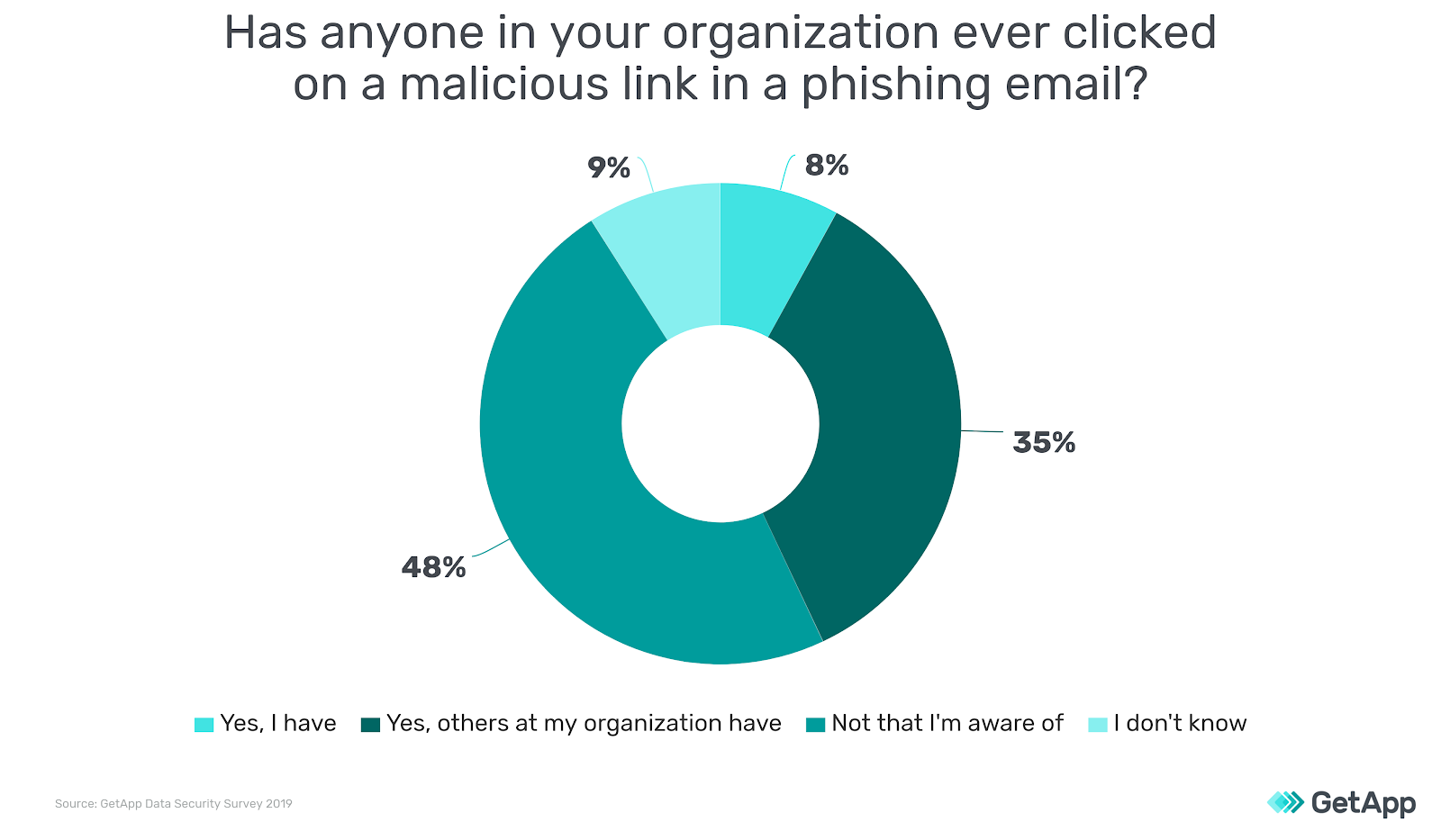
43% of employees admit someone in their organization has clicked a link in a phishing email
Phishing is an email scam that dupes individuals into clicking a malicious link or downloading a malware-laden attachment. Traditional phishing attacks are low success endeavors because hackers send out thousands of emails with the hope that a few are successful.
However, targeted phishing attacks—known as spear phishing—are increasingly common and far more effective. That's because spear phishing emails appear to come from a trusted party and are aimed at specific individuals or organizations, causing recipients to lower their guard. Our survey found that 8% of respondents have clicked a malicious email link while another 35% knew of others in their organization who had done the same.
Recommended reading:
24% of businesses have been victimized by a phishing attack
Nearly a quarter of the respondents in our survey reported that their organization has been victimized by a phishing attack. Phishing schemes result in numerous consequences, including malware installation, the compromise of account credentials, and the transmission of sensitive data. Successful phishing attacks can also expose companies to ransomware or result in identity theft.
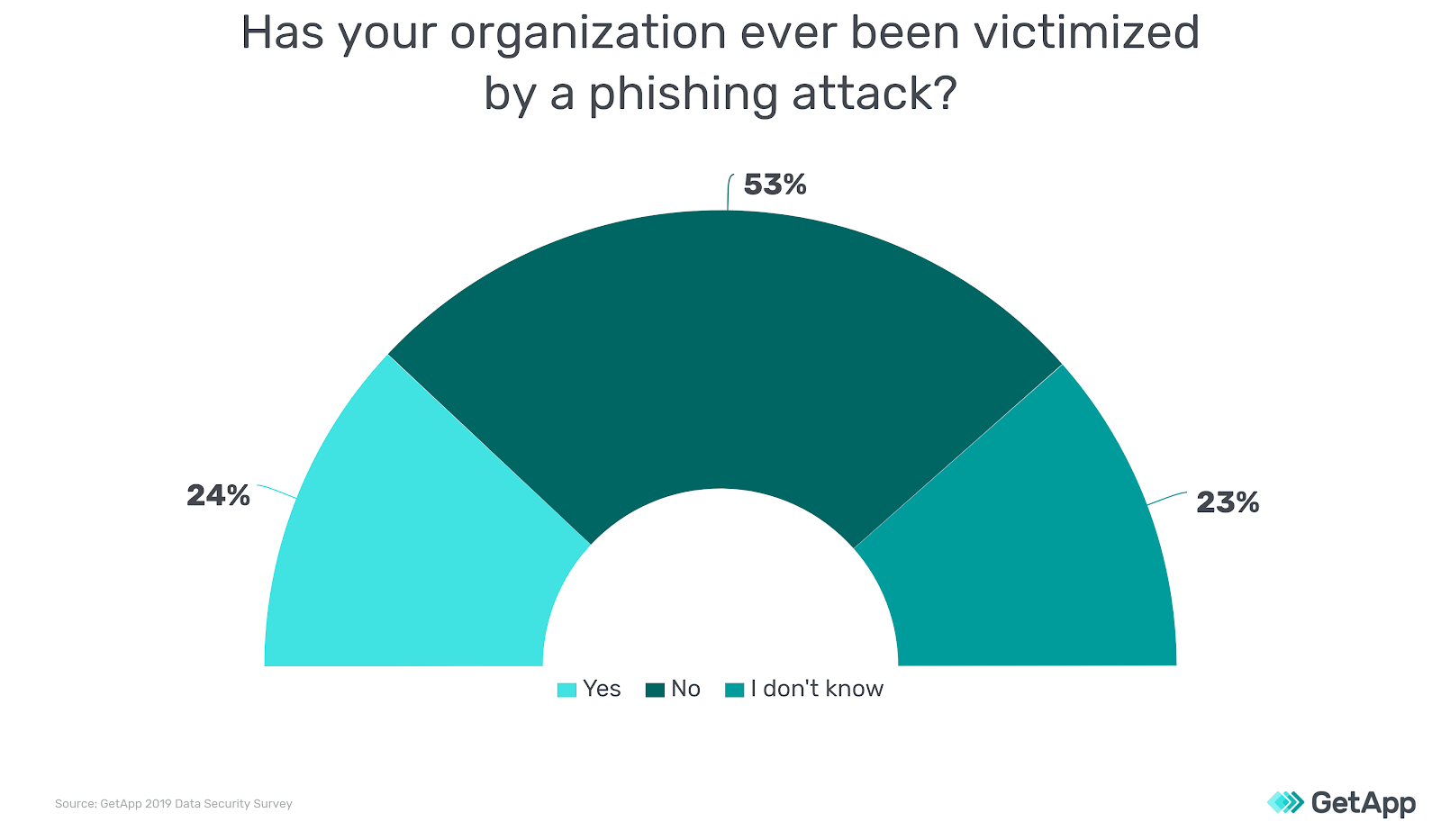
And while nearly 1 out of 4 businesses reporting successful phishing attacks is concerning, the actual number might be higher. Phishing ploys are often used in the first step of an advanced persistent threat (APT) whereby security is quietly breached to gain privileged system access. APTs are used by hackers to quietly monitor systems or steal data over an extended period of time. Therefore, it may be that a phishing attack is successful, but the victim never finds out—or realizes far too late.
Only 64% of businesses report using two-factor authentication
Authentication tools verify the identity of those seeking access to business data. Two-factor authentication (2FA) strengthens basic username/password authentication methods by requiring a secondary authentication method, most commonly a verification code sent to a mobile device.
2FA is key to keeping your business from becoming another phishing statistic. Many phishing schemes lead the victim to a bogus password reset page where they are asked to enter account credentials. Without 2FA, the cybercriminal can instantly use the stolen credentials to violate the account. However, if 2FA is enabled, the compromised account will require a secondary means of identification, such as a passcode sent to a phone.
Our survey revealed that nearly two thirds of organizations use 2FA for business applications. While this is generally encouraging, it also means that more than one third could be incurring unnecessary business risks by overlooking such an effective and simple security measure.
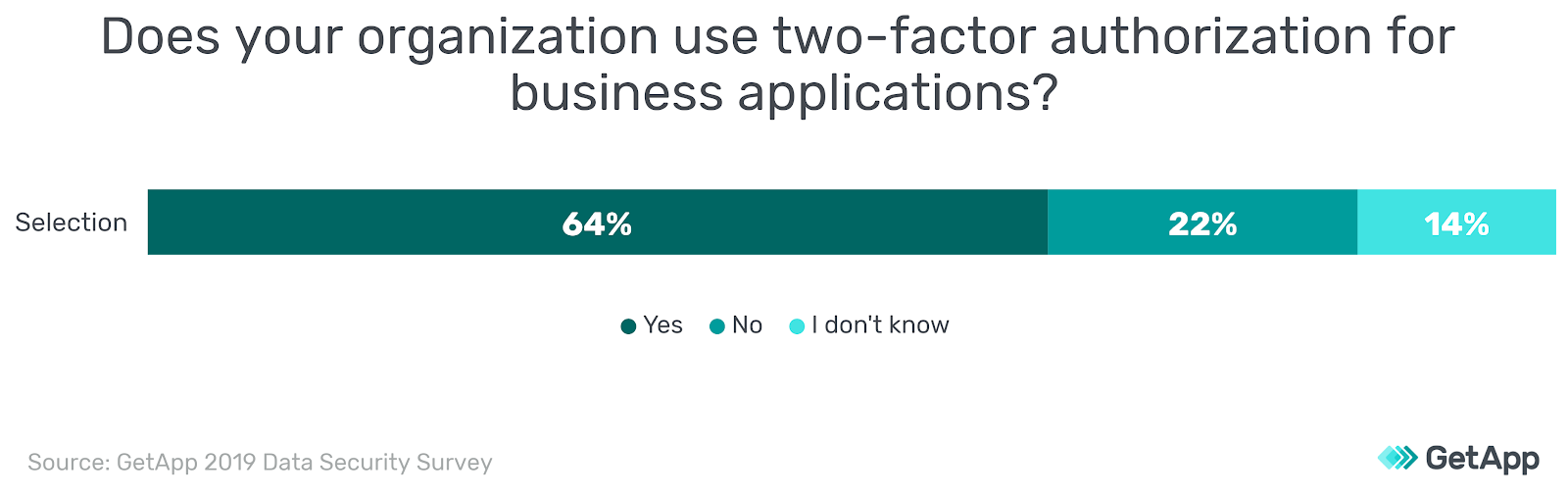
Every business application should have 2FA enabled. Strong authentication measures are especially important on email accounts and any application or device that allows remote access. And while it's true that 2FA can still be compromised by a determined hacker, it's substantially more secure than a single password and should be considered the minimal standard for the protection of business data.
Only 27% of companies provide social engineering training
Phishing schemes use social engineering techniques to exploit human nature. Cyber criminals commonly research organizations prior to sending spear phishing emails or target innate human characteristics such as the tendency to follow directions. Unfortunately, our survey found that only 27% of businesses provide social engineering awareness training for their employees.

Companies must prepare employees to recognize social engineering methods designed to steal sensitive company data. Social engineering training can be part of your data protection training or—perhaps more effectively—designed as a standalone session that explains the methods cyber criminals use to deceive employees. And because these techniques are always evolving, it's important to update training sessions and hold them on a regular basis.
Recommended reading:
Only 30% of companies conduct phishing tests
Phishing tests are an effective means of determining how vulnerable employees are to fraudulent email schemes. These tests can be designed by your IT security team, carried out by a third party company, or purchased as a software product. They are designed to simulate real phishing attacks and promote awareness of how they are carried out.

Phishing tests should always be employed with care and followed by security awareness training. Keep in mind that the worst reaction to a failed phishing test is to punish an employee who already feels tricked. Punitive action will only cause resentment and might even make the employee less likely to report accidental breaches in the future. Instead, focus on positive reinforcement for those who do well and consider a reward system for those who accurately identify phishing emails or other cyber security threats.
Test yourself with Google's Jigzaw phishing test here.
Putting phishing statistics in perspective
Our phishing statistics show that most companies are still facing considerable threats from phishing schemes. The good news is that there are many strategies available to mitigate these threats.
Companies must improve basic security hygiene by implementing 2FA where available. They must also employ phishing tests and conduct social engineering awareness training so that employees understand the tactics they're up against and how they can better protect company data.
Need email security software to help prevent phishing attacks?
Methodology
The cybersecurity statistics referenced in this article resulted from a survey that was conducted by GetApp in June, 2019, among 714 respondents who reported full-time employment in the United States.
*This document, while intended to inform our clients about phishing statistics, is in no way intended to provide legal advice or to endorse a specific course of action.


