
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
How multi-factor authentication options keep small businesses secure
Nearly half of all cyber attacks target small businesses. Most small business owners know that they’re not safe: the majority of them list cybersecurity threats as one of their top concerns.
With the sheer number of cyber attacks on the rise-the FBI estimates that 4,000 ransomware attacks, alone, occur per day-you should start thinking now about how your small business can improve your IT security.
Until now, a popular and more easily implementable method of preventing cyber attacks has been two-factor authentication (also known as 2FA). But as cyber criminals’ methods grow more sophisticated, two-factor authentication has been found to be lacking in its effectiveness.
The good news is that there’s still a way to ensure that your data stays safe, even if you don’t have the time or resources to revamp your entire cybersecurity plan. Implementing multi-factor authentication (MFA), will literally add at least one more layer of security for hackers to get through.
What is multi-factor authentication?
Multi-factor authentication is a reaction to the vulnerability of existing two-factor authentication methods.
The idea behind two-factor authentication is the oft-repeated phrase of using “something you know and something you have” to access data, programs, hardware, and software. For example, to access your bank account online you have to not only enter your password (something you know), but also enter a PIN code generated from a security device (something you have).
With multi-factor authentication, you can change that phrase to “something you know, something you have, and something else, just in case.”
Ultimately, the idea behind multi-factor authentication is that, the more steps a user has to take to gain access to sensitive information or complete a transaction, the harder it is for hackers to exploit this process.
Multi-factor authentication uses many of the authentication methods you’re likely already familiar with if you use two-factor authentication. A username coupled with a password, for example, is one of the most common methods of user identification. Verification codes sent via email, SMS, or an entirely independent authentication app are often used as a second layer or defense.
With MFA, you can add a number of authentication methods to the mix, but the latest fad in identity management is adding a piece of hardware, known as a token, to a sign-in process. A token could be a card a user swipes, a fob they present, or a USB device that generates a password when it’s plugged in to your computer.
The use of hardware-based tokens, especially, are a reaction to the ability of cybercriminals to crack weak passwords or security questions and intercept 2FA codes sent via SMS or email. While your mother’s maiden name might be easy to find after digging around on Google, a hacker is much less likely to be able gain access to a piece of equipment you have in your possession.
Avoiding common MFA adoption problems
If you think using multi-factor authentication is the right move for your business’s data security, I don’t blame you. Protecting sensitive information is important for both your business and your customers. However, there are a obstacles you might run into when implementing MFA, which I’ll discuss below.
Employee adoption
The perceived ease-of-use of any business software you adopt has a lot to do with how many employees are going to use the system correctly. No one wants to use a system that makes their daily tasks more complicated. While you can preach the importance of stringent cybersecurity measures until you’re blue in the face, your non-technical employees aren’t going to use a program that doesn’t work well.
Especially when it comes to cybersecurity, where a company’s employees are often considered their weakest link, it’s important to consider any multi-factor authentication program you might adopt from their perspective first. If there’s an easier way to access data and hardware without jumping through a million hoops, you can bet your employees will find it and use it instead.
Takeaway: Consider any MFA system you choose from a user perspective and not just a security perspective. Remember that if your employees don’t adhere to new security measures, they’re not protecting you anyway.
MFA programs aren't cheap
If you’re investing in tokens for each employee, you might find the cost of a multi-factor authentication system mounting. Implementing an MFA strategy can involve a significant invest of time-as I mentioned above with employee adoption-and money.
While the up-front cost of multi-factor authentication might seem expensive, keep in mind that the average cost of a data breach for a small business reached $117,000 in 2017. While not investing in sufficient IT security measures might initially seem like a good idea for your account balances, a cyber attack will destroy any sense of financial security you were holding on to.
Takeaway: The cost of a security breach, in terms of both your funding and your organization’s reputation, far outweighs the cost of providing adequate security for your business.
You still need a backup plan
Since MFA-and even 2FA-rely on a user having something in their possession to prove their credentials, you have to account for human error. What if your employee leaves their smart phone at home? What if they lost the card they need to swipe? Not only does implementing MFA require coming up with a new security strategy, it also requires have a strategy for when your new strategy doesn’t work.
Takeaway: No security plan is perfect. Prepare as much as you can for when-not if- something will go wrong, including employee error.
Some examples of multi-factor authentication solutions for small businesses
In order for you to get a few ideas of what actual software that utilizes MFA is like, we’ve put a few examples below of apps that specialize in MFA. This is in order to give you an idea of not only what MFA features would be offered in a typical solution, but also some of the other features that the app might utilize.
OneLogin

Using OneLogin’s own authentication app (OneLogin Protect), users can verify their identities via their smartphones. It also integrates with other third-party authentication factors like Google Authenticator and Yubico’s YubiKeys and provides a single sign-on option for your company desktops.
Duo Security

Duo Security is best known for its two-factor authentication solution, but it also has an MFA option for those who want to implement more layers of security. Like OneLogin, Duo also has its own authentication app (Duo Push). Duo works with both smartphones and tokens for identity verification methods.
ThisData
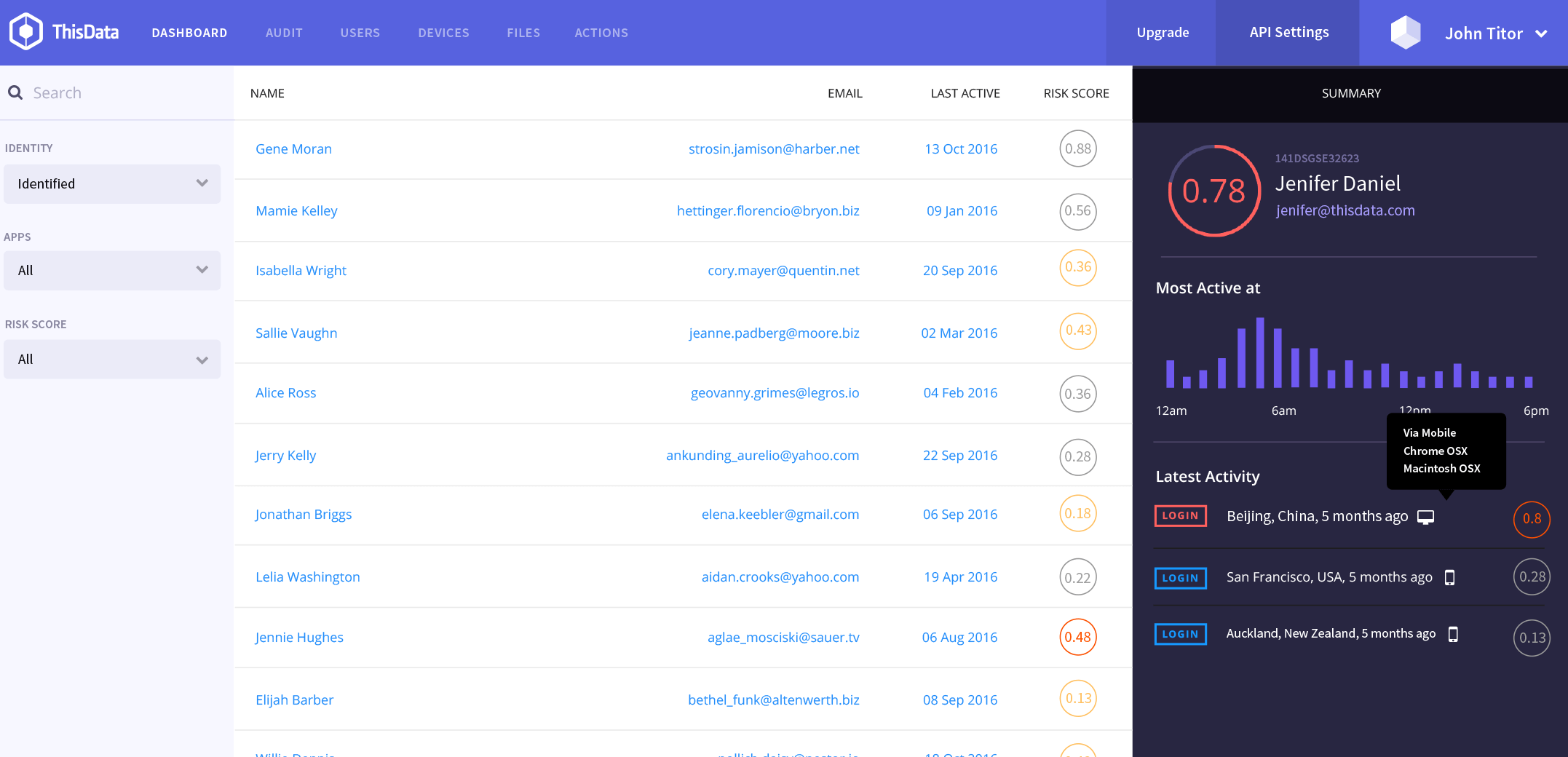
ThisData offers a two-factor authentication solution in addition to a continuous authentication strategy. Continuous authentication means that users are prompted to sign in at login, as well as at different times throughout an application’s use. You can think of it like being prompted to enter your PIN when attempting to complete a second transaction at an ATM.
What now?
Remember: implementing a multi-factor authentication strategy is only one piece in the puzzle of IT security. While focusing on your non-technical employees is often the easiest fix for your cybersecurity weaknesses, considering your overall network security and data backup strategies is also a good call. As we’ve seen with MFA, when it comes to IT security, the more layers you have, the better.
For more information on security, also check make sure to check out:
GetApp's IT Management and Security categories
