
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
A 7-Step Penetration Testing Guide by a Security Director
Grasp the process of identifying and fixing hidden vulnerabilities that hackers could exploit to breach your small business.

For small-business IT managers with limited resources, a poorly executed penetration test is worse than none because of the false sense of security it might yield. To avoid this, you can hire an external partner to uncover hidden vulnerabilities without disrupting your IT systems.
That's the advice of Colleen Morrissey [1], acting director of information security at Rensselaer Polytechnic Institute, who says employing external experts not only guarantees thorough testing but also eliminates potential conflicts of interest that could arise if the same people who secure the systems are also testing them. More of Morrissey's insights in this step-by-step guide will help you feel confident about taking on penetration testing.
"Every penetration tester, aka ethical hacker, has their own style. Some provide remediation after the test, and some don't. Knowing all the steps helps negotiate your service package with your pentesting partner."
—Colleen Morrissey, Acting Director of Information Security at RPI

Colleen Morrissey, Acting director of information security at RPI
Before beginning with the steps, it’s essential to decide which penetration testing technique will work best for your company’s vulnerability identification process.
3 techniques of penetration testing
Although penetration testers decide this themselves, your business’s nature, requirements, and budget also determine which technique would be followed to uncover the maximum number of vulnerabilities.
1. Manual penetration testing
In a manual penetration test, cyber security experts dive into your systems, using their intuition and experience to think like a hacker. They explore "what if" scenarios that automated penetration testing tools may overlook, manually trying sequences to exploit complex vulnerabilities.
Manual tests, while time-consuming and costly, offer deep insights, making them ideal for businesses with complex and unique IT infrastructures. Morrissey advises this method if you have sensitive data or unique systems that automated tools might not fully cover.
2. Automated penetration testing
Automated penetration testing is like setting a robot to work on your system. These software tools conduct a simulated attack to scan your networks, websites, and applications for known security weaknesses. However, they're limited to known issues stored in their database, and can't think outside the box like a human.
Morrissey says automated tools are ideal for businesses with standard IT setups and limited budgets. They offer speed and cost-efficiency, providing a broad overview of potential vulnerabilities. But if you rely heavily on unique software or proprietary systems, don't solely rely on automated tools.
3. Combination of manual and automated processes
Combining manual and automated testing offers the best of both worlds. Automated tools quickly identify known vulnerabilities, while manual testing dives deeper into potential issues.
A combination of manual and automated testing offers a comprehensive security assessment, ideal for most businesses, according to Morrissey. It leverages the speed of automated tools and the depth of manual testing. However, for very small businesses with simple IT setups, it might be more than what's needed. Balance the cost with your specific cybersecurity needs.
Penetration testing approaches to form a better overall strategy
Morrissey says there are three approaches to conducting penetration tests—Black Box testing, White Box testing, and Grey Box testing.
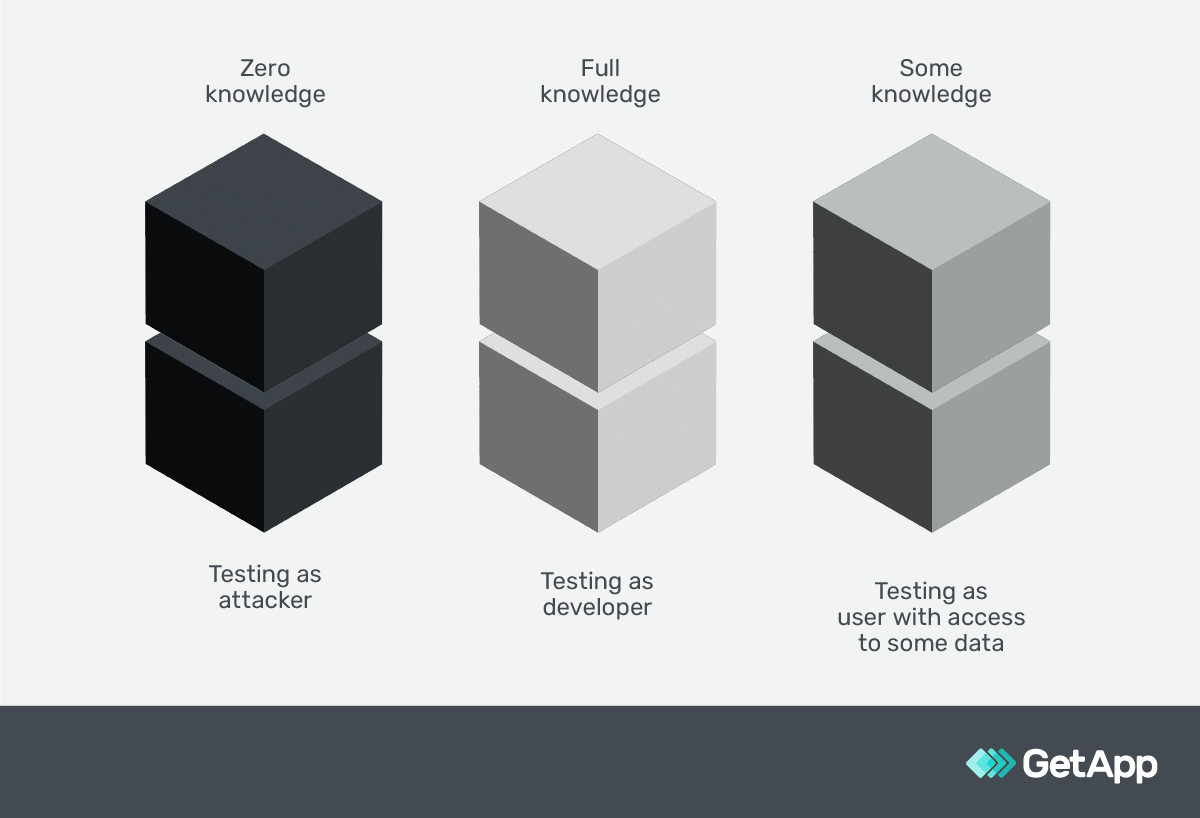
Knowing these approaches helps you and your security team pick the right strategy that aligns with your business's unique needs and circumstances. Learn about them and nine unique types of penetration testing here.
How to do penetration testing in seven steps
Step 1: Plan and define rules of engagement
Morrissey describes the planning phase as when pen-testers establish the scope and objectives of the test. This involves identifying key areas of concern, such as specific systems or applications, and outlining the boundaries of the test, like timeframes and any off-limits areas.
They set goals such as discovering vulnerabilities that could lead to data breaches or unauthorized access. For instance, they might focus on your company's web applications, searching for vulnerabilities such as SQL injection or cross-site scripting (these are types of cyber attacks that inject malicious code into your web apps), which could enable a data breach.
Pro tip
Choose a penetration testing partner who believes in a clear and transparent planning process. Using project planning software will ensure that everyone is aware of the testing scope and objectives. This could be as simple as sharing the test plan with all involved parties via the software, which can also facilitate real-time updates and communication.
Step 2: Gather necessary information with proper scrutiny
In the reconnaissance phase, pen-testers gather extensive information about the target system and the company’s resources, including employees. They start by understanding the system's architecture and identifying potential entry points for hackers. For instance, they may take note of the software versions your web applications are running on. Outdated software can have known vulnerabilities, such as unpatched security flaws or end-of-life software that no longer receives updates. By focusing on these details, the pen-testers can identify weak points that might be exploited.
Pro tip
Encourage your penetration testing partner to utilize open source intelligence (OSINT) platforms such as search engines, public databases, and social networking sites. These platforms are effective in unearthing public information, such as your organization’s social media posts that could reveal details about the IT infrastructure, or details about your employees and their roles.
This information can shed light on potential vulnerabilities and can be exploited in social engineering attacks. By leveraging publicly available information, your penetration testing partner can mimic the tactics of real-world attackers, helping you better understand and secure your digital footprint.
Step 3: Discover and tally all the vulnerabilities
During the discovery phase, Morrissey says that pen-testers actively hunt for vulnerabilities using a combination of vulnerability assessment tools and manual techniques. These tools could be network security scanners or web vulnerability scanners, while manual techniques might involve analyzing application logic or testing password policies. The focus could be on identifying less common, but equally dangerous vulnerabilities, such as insecure direct object references (a flaw where users can access unauthorized data) or server misconfigurations.
Pro tip
Ask your penetration testing partner to not just list out vulnerabilities, but also prioritize them based on the risk they present. For instance, a vulnerability that exposes sensitive customer data should be given higher priority than a minor misconfiguration that has limited potential for exploitation. This will help you address the most-critical threats first and use your resources effectively.
Step 4: Actively exploit discovered vulnerabilities
During exploitation, pen-testers play the attacker's role and exploit the identified vulnerabilities to understand their impact on your small business operations. Morrissey shares an instance, where your pen-testers might try to bypass authentication controls to access restricted areas of your application. By doing this, they understand each and every step a hacker could take to potentially exploit those vulnerabilities.
Pro tip
Documentation is crucial at this stage. Make sure your penetration testing partner meticulously records each step of their exploitation process. This can be done by using IT documentation software, which helps in creating detailed and clear records.
This documentation is important because it provides a clear trail of the tester's actions, their findings, and the extent of potential damage, which is vital when devising remediation strategies.
Step 5: Explore the compromised systems post-exploitation
After exploiting detected vulnerabilities in your system, pen-testers mimic potential intruders, gauging the extent of possible damage. According to Morrissey, they might inspect the type of sensitive data they can access, such as customer information or financial records.
They may also see if they can manipulate other parts of the system, such as gaining control over user accounts or altering network configurations. This exploration helps them understand what a real attacker could potentially do, uncovering additional areas of your infrastructure where your security measures need to be strengthened.
Pro tip
Check if your penetration testing partner utilizes threat intelligence tools during this phase. These tools can provide insights into how real-world attackers might maneuver within your system, such as exploiting certain vulnerabilities to gain administrative privileges or using lateral movement to access other interconnected systems. Understanding these can help you build stronger defenses, such as enhancing user account security or segregating your networks to limit an attacker's reach.
Step 6: Check reports and recommendations
Once the testing concludes, pen-testers thoroughly compile their findings and remediation suggestions into a comprehensive report. The report typically includes the vulnerabilities discovered, their potential implications (such as data loss or system disruption), and a remediation plan to address them. This detailed and systematic reporting helps you understand the risks and prioritizes them for action, Morrissey adds.
Pro tip
As an owner, you should expect a well-structured and actionable report from your penetration testing partner. They should ideally use professional report generation tools, which can help in creating a well-organized, easy-to-understand report.
Additionally, don't hesitate to request clarification or additional information if any part of the report is unclear. It's essential that you fully understand the findings and the steps you need to take next.
Step 7: Remediate and re-test the systems
If it's included in your service package, pen-testers will assist in addressing the vulnerabilities they've identified. They might patch software, adjust security configurations, and then re-run the vulnerability scans to verify the effectiveness of the fixes. This is much like repeating the discovery phase but with a focus on the areas previously found to be vulnerable.
Pro tip
Remember that remediation isn't a one-and-done task. New vulnerabilities can emerge as systems and threats evolve. Look for a penetration testing partner who can offer ongoing support and advice even after testing. This can help you stay ahead of potential security issues in the future.
Check these tips off your list before signing a contract with a pentesting partner
Who you are hiring for this job can make or break your company’s IT infrastructure. Here are some tips:

After signing a contract and onboarding a partner, you wouldn't want to be the business owner with insufficient knowledge to be tricked into higher prices. Do your homework. Download GetApp's security assessment template below to get up to speed with where your company is vulnerable and where you can be affected.
This will help you understand what and how your pentesting partner works on your IT infrastructure systems and empower you to collaborate with them efficiently.
Sources
Colleen Morrisey, LinkedIn

Bhavya Aggarwal

