
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
Cybersecurity Best Practices for Your Small Business
From using strong passwords to training employees on security threats, here are the best cybersecurity practices small businesses are adopting to protect themselves against existing and emerging threats.

Cybersecurity has never been more important. Many business processes have moved online, and because of this, no organization is safe from cyberattacks. The problem only increases for small businesses like yours, given you have a limited budget for cybersecurity and fewer employees that are able to keep tabs on security-related measures.
But there's much you can do on a small budget as well. Training your employees on cybersecurity awareness and using standard security measures are some practices that can help your small business prevent a cyber attack to a large extent.
In this article, we discuss the top five cybersecurity best practices small businesses such as yours should adopt. We asked small-business leaders about the measures they follow and have used their responses to make relevant suggestions for your small firm. We also analyzed GetApp’s 2021 State of Data Security report [***] to identify trends and themes small businesses like yours should be aware of.
Top 5 cybersecurity best practices for your small business

1. Use strong passwords and two-factor authentication
Passwords play a far more important role in securing your business applications than you think. Strong, unique passwords that have a combination of letters, numbers, and symbols are effective in preventing cybersecurity risks such as brute-force attacks in which cybercriminals try hacking your systems or applications by guessing different username-password combinations.
However, 60% of our respondents admit to reusing the same password for multiple accounts, putting themselves and their company at risk of an account takeover.
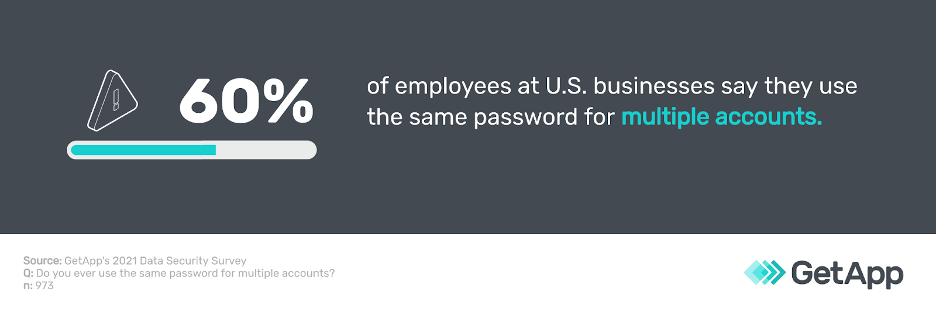
Our research also shows that account takeovers are three times as likely among those who reuse passwords compared to those that use unique passwords every time.
To protect your applications and company data further, use two-factor authentication (2FA). 2FA requires your employees to authenticate themselves via a second security method—an OTP, a security question, or biometrics—besides their username and password. 2FA doubly secures your applications and helps prevent identity thefts.
In GetApp’s 2020 State of Data Security survey [**], 82% of responding businesses said they currently use 2FA for some or all of their applications. Kit Barker [1], chief technology officer (CTO) at myhrtoolkit.com, perfectly summarizes the use of passwords and multistep authentication.
For every system you use you need to have a very strong password and enable multifactor authentication (MFA or sometimes called 2FA). MFA drastically reduces the likelihood of an account being compromised.
—Kit Barker, CTO at myhrtoolkit.com
Barker also recommends using a password manager, which safely stores your employees’ passwords so they don’t have to remember multiple passwords for various accounts. They need to remember only the master password, which can unlock all other passwords.
Interested in finding top-rated password manager software? Check our directory.
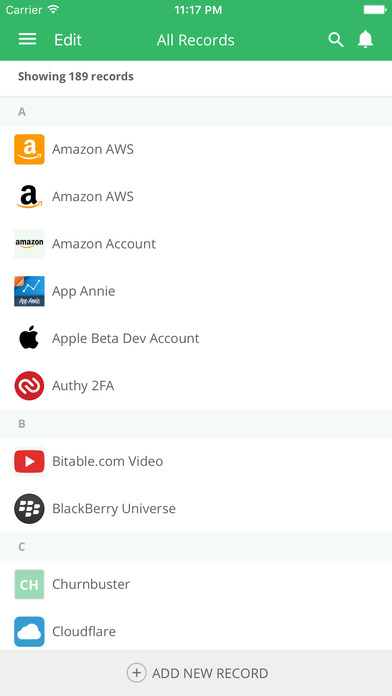
TeamsID software saving the passwords of multiple accounts on a mobile device (Source)
2. Don’t click on any suspicious email links
Phishing emails are one of the most common types of cyberattacks. These emails seem to be from legitimate sources (e.g., a company you know or trust), but they contain malicious links or attachments, which, if clicked on, can lead to a full-blown malware attack or security breach.
And they’re getting increasingly sophisticated.
In GetApp’s 2020 State of Data Security survey [**], 80% of respondents reported receiving phishing emails, of which 58% admitted to clicking a malicious link in the email. While the frequency of phishing emails have stayed relatively consistent since 2019, our 2021 Data Security survey [***] shows that the number of people clicking on a malicious link have increased.
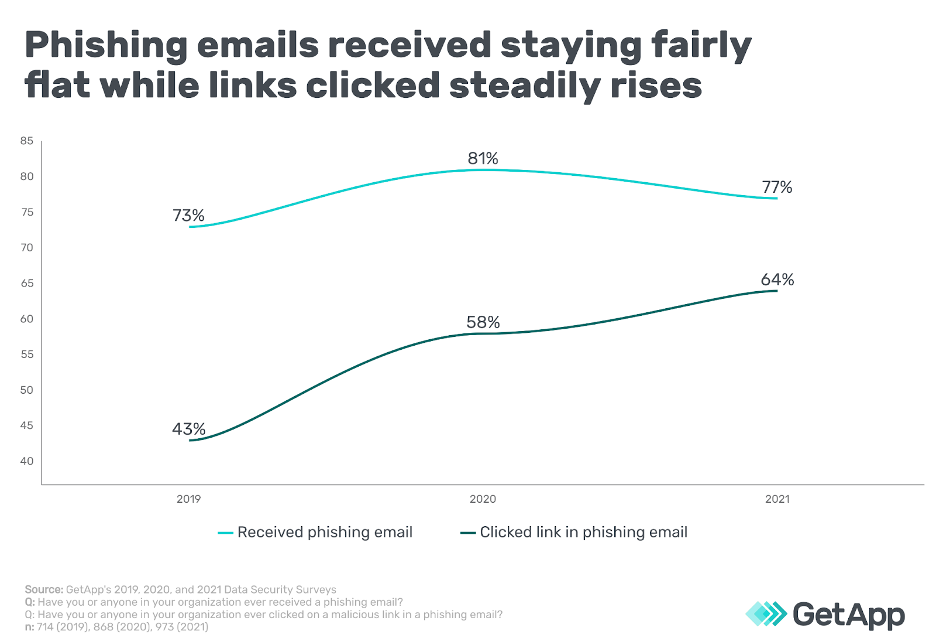
This is likely because phishing emails have become more targeted, using realistic logos, professional grammar, and are personalized to the recipient. Since no technology can perfectly identify phishing emails, training your employees on cybersecurity awareness is your best bet. 31% of companies do not train their employees annually. Nick Santora [2], CEO of Curricula, shares a similar sentiment. He says training employees on potential phishing scams, ransomware attacks, and what to look out for in suspicious emails is the most effective cybersecurity practice for organizations.
Need help training your employees on how to spot phishing emails? Here’s a handy guide we’ve prepared for you.
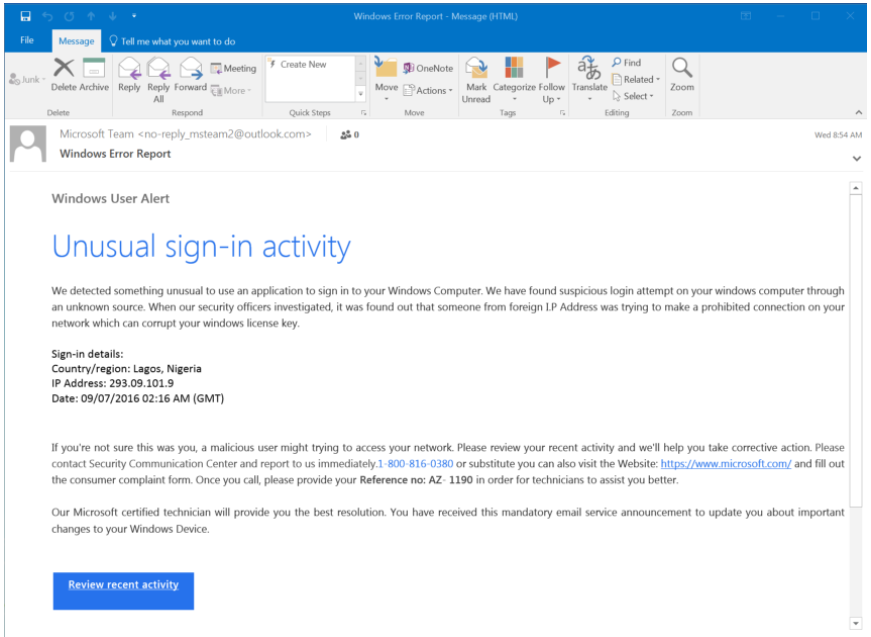
A sample phishing email (Source)
3. Install software updates immediately, and back up your data regularly
Every time a software update is available, you should receive a system notification to download and install it. At times, you may even have to restart your system to install the update, which can be a nuisance, especially if you’re in the middle of important work. But you should pause all your work and immediately install any available update.
That’s because most of these updates contain security patches to existing software vulnerabilities, which, if left unpatched, can be exploited by a hacker to break into your system or application. A study [3] has found that 27% of data breaches faced by organizations are caused by unpatched vulnerabilities.
Instruct your employees to install software updates as soon as they receive a notification. Kristen Bolig [4], founder of SecurityNerd, says regularly updating computers and work-related apps, is a cybersecurity practice every employee at her company follows.
Besides updating your software, you must also back up your data regularly. Regular data backups will help you recover sensitive data and ensure business continuity in the event of a security incident such as a data breach or loss. Here are some market-leading data backup software tools you can consider purchasing.
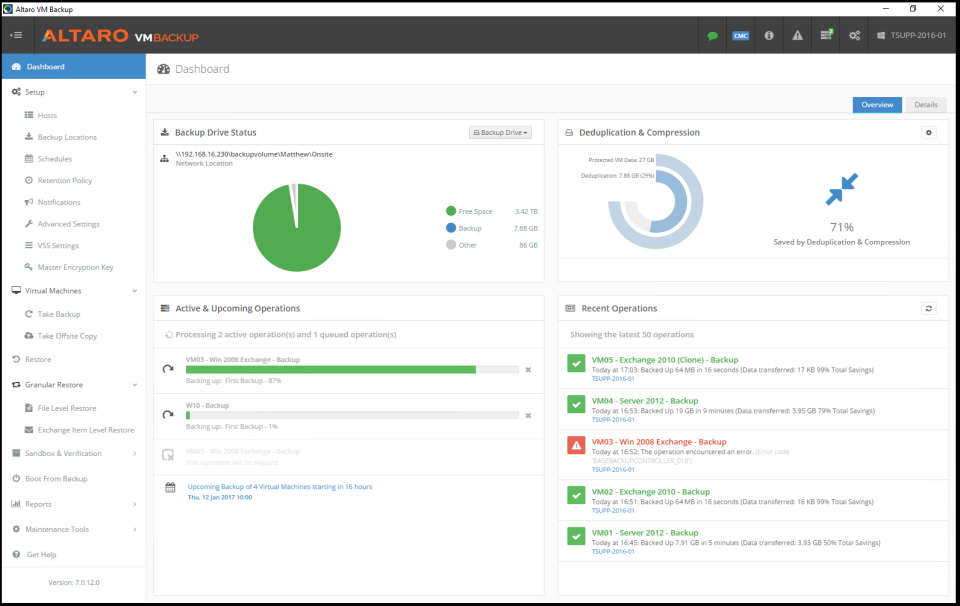
Tracking the status of data backups in Altaro VM Backup (Source)
4. Use network protection tools to secure your networks
According to our 2020 State of Data Security survey, after remote work security, network security is the second biggest security vulnerability faced by businesses. Network security involves protecting components of your computer network such as routers, servers, network operating systems, and other software resources connected to the internet or intranet.
As a small business, you may overlook network security due to inadequate resources or expertise, but with the right tools, you can protect your network from unauthorized access. For starters, use a VPN, a firewall, and a basic network monitoring tool. Also, encrypt in-transit data to protect it from hackers trying to intercept data moving between network points.
If you need assistance with strengthening your network security, partner with a network security provider. Here are some resources to help you learn more about network security:

Network monitoring status in LogicMonitor software (Source)
5. Take security training seriously
If you invest in security technology but don’t train your staff on cybersecurity, you won't reap the best results. Businesses like yours are not only prioritizing security awareness training but also using new methods to make training more interesting for their employees.
In GetApp’s 2020 State of Data Security survey [**], 71% of respondents reported undergoing security training at least once a year. They also said they receive training via unconventional methods such as webinars (46%) and AR/VR sessions (17%). Thierry Tremblay [5], CEO and founder of Kohezion, stresses the importance of cybersecurity training.
My number one cybersecurity tip is to educate all employees continually. No matter what kind of sophisticated technology you use to protect your data, employees are still the most common entry points for attackers and phishers. Cybersecurity training strengthens the most vulnerable link in your cybersecurity chain.
—Thierry Tremblay, CEO and founder of Kohezion
Make sure your employees know how to identify a phishing email, are up-to-date with ways to stay safe online, and know how to securely back up and access data, especially when working remotely.
You can also visit our training software directory to select software that can help automate training processes for your small business.
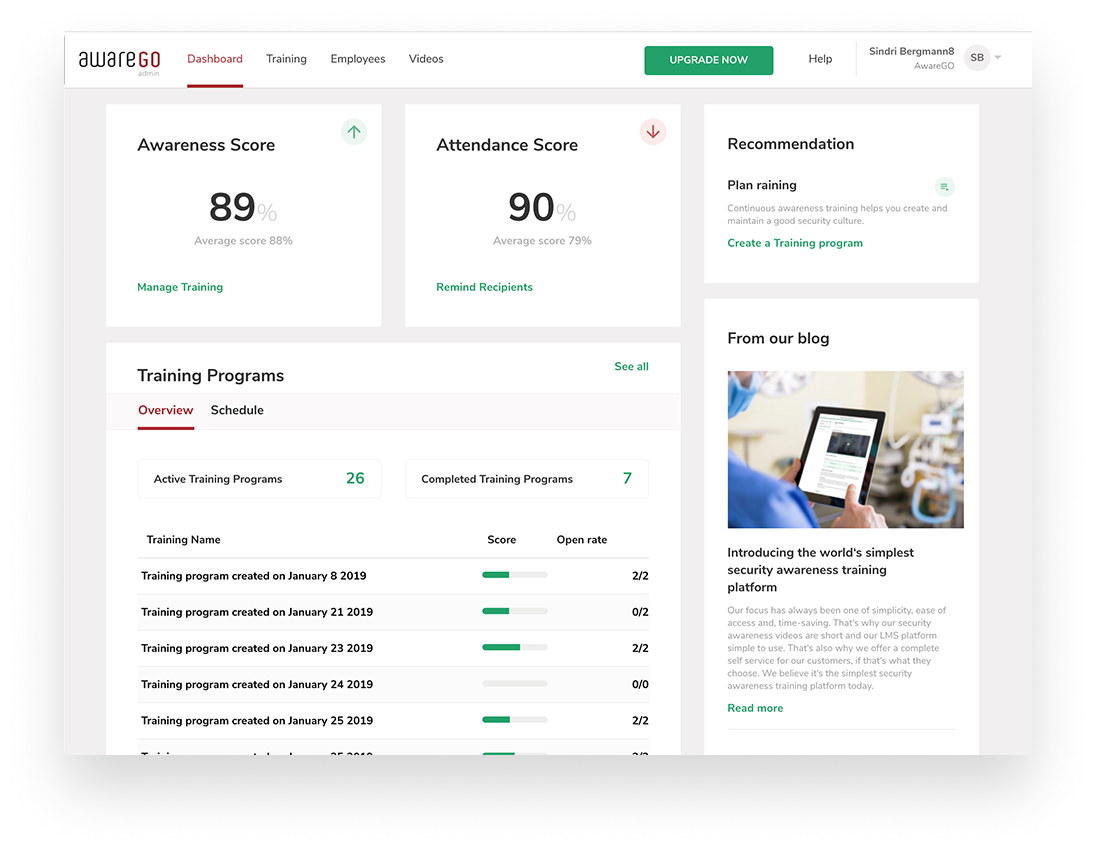
Tracking security programs and their scores in AwareGo (Source)
Simple cybersecurity practices will keep your small business safe
We often associate cybersecurity with sophisticated technologies such as AI-based threat detection and risk assessment. But the truth is, simple techniques such as using strong passwords and training your employees to remain vigilant are equally effective in mitigating cyberattacks. The absence of basic cybersecurity hygiene is, in fact, what leads to a data breach.
It’s often the absence of basic safeguards that result in cybersecurity risks. Diligently follow the cybersecurity best practices we’ve shared in this article and use our suggested security software tools to further strengthen your cybersecurity framework.
Additional resources:
Methodology and disclaimer
* GetApp’s 2019 Data Security Survey was conducted in June 2019 among 714 respondents who reported full-time employment. Of the 714 respondents, 207 identified as IT professionals.
** GetApp’s 2020 Data Security Survey was conducted from September 10 to September 11 among 868 respondents who reported full-time employment. Of the 868 respondents, 267 identified as IT professionals and 83 identified as their organization’s IT security manager.
*** GetApp’s 2021 Data Security Survey was conducted from August 20 to August 24 among 973 respondents to learn more about data security at U.S. businesses. Respondents were screened for full-time employment and 90 identified as their organization’s IT security manager.
Note: The applications selected in this article are examples to show a feature in context and are not intended as endorsements or recommendations by GetApp. They have been obtained from sources believed to be reliable at the time of publication.
Sources

Toby Cox

