GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
How To Create a Cybersecurity Incident Response Plan
Here are five simple steps to help you create a cybersecurity incident response plan for your organization.

What would you do if your company faced a cybersecurity incident? Do you have an action plan to respond to events such as ransomware attacks, data breaches, or DDoS attacks? If not, it’s time to strengthen your cyber defenses.
In this article, we’ll discuss what a cybersecurity incident response plan is and how it benefits you. We’ll explain the five steps to create your incident response plan as well as provide some resources to help you get started.
What is a cybersecurity incident?
A cybersecurity incident is any event that violates an organization’s IT security policies and puts sensitive data such as customers’ financial details at risk. Malware infections, DDoS attacks, ransomware attacks, unauthorized network access, insider attacks, and phishing are some common types of cybersecurity incidents.
What is a cybersecurity incident response plan?
A cybersecurity incident response plan is a set of instructions to help your staff members identify, respond to, and recover from cybersecurity incidents.
Most incident response plans include the security measures you should follow to prevent a cyberattack as well as the steps to take when you’re faced with an attack. They also outline the various steps your staff should follow immediately after an attack, such as informing stakeholders or reporting the incident to government officials.
Why do you need a cybersecurity incident response plan?
Here are the key reasons you need a well-documented and regularly updated cybersecurity incident response plan.
You’ll be better prepared to handle cyberattacks
With a cyber incident response plan, you and your team members will know what to do once a security incident is reported or communicated. Everyone will have a well-documented role and responsibility. You won’t have to give additional instructions to your team, so there’ll be no time lost or communication gaps.
You’ll be complying with regulations
In the event of a security incident, you’re supposed to follow many requirements, such as informing stakeholders and reporting the incident to authorities. A response plan will help you keep track of and comply with these requirements. For instance, consumer data protection law GDPR mandates that you report a security event within 72 hours of its occurrence, while financial information security standard PCI DSS requires you to have an incident response plan and test it at least annually.
You won’t have to rely on ad-hoc incident response measures
A cybersecurity incident response plan is a written document that clearly states the steps you and your staff are supposed to follow when faced with a security breach. It’s approved by company management, which means you won’t have to rely on any unplanned decisions. A prepared response is more effective than an ad-hoc, chaotic response, especially in urgent situations such as identity theft.
5 steps to create your cybersecurity incident response plan
Before we get started, remember that communication is key. To lay the groundwork for an incident response plan, Gartner finds that you need to ensure all stakeholders understand their responsibilities and agree on project expectations (full content available to clients).
Here are five broad Gartner-recommended steps to build a cybersecurity incident response plan that’ll help you identify, contain, remove, and recover from security incidents.
1. Document the common types of security incidents
Create a document that lists the different cybersecurity threats your business is vulnerable to. This document will help you prepare different response strategies for different cyber incident types.
The below table lists some common types of cybersecurity incidents.
| Incident type | Description |
|---|---|
| Malware | Malicious software (viruses, worms, trojans, etc.) that gets unauthorized access to your systems and disrupts operations. |
| Distributed denial of service (DDoS) | Makes your online service (e.g., website) unavailable by overwhelming your server with more traffic than it can handle. |
| Phishing | A social engineering attack that dupes users to believe malicious emails as legitimate. |
| Web application attack | Attacks your web applications such as shopping carts, online forms, and word processors to gain access to your databases and steal sensitive information. |
| Insider threat | Current or former employees violating IT security policies to gain unauthorized access, leak confidential data, or damage systems. |
| Loss or theft of equipment | Lost or stolen company PCs, laptops, or mobile devices that can be misused to steal data or launch a full-fledged cybersecurity attack. |
2. Prioritize security incidents based on their severity
Security incidents differ by magnitude and severity. A corrupted file on your employee’s laptop can be considered a low priority compared with a DDoS attack that can bring down your entire website. Determine the severity of every security incident to decide if it should be resolved on priority.
A good way to do that is assessing if the incident affects your data (makes it inaccessible, steals data, or results in data loss) or your ability to serve clients or run operations. Any incident that affects both data and operational security should be addressed on priority.
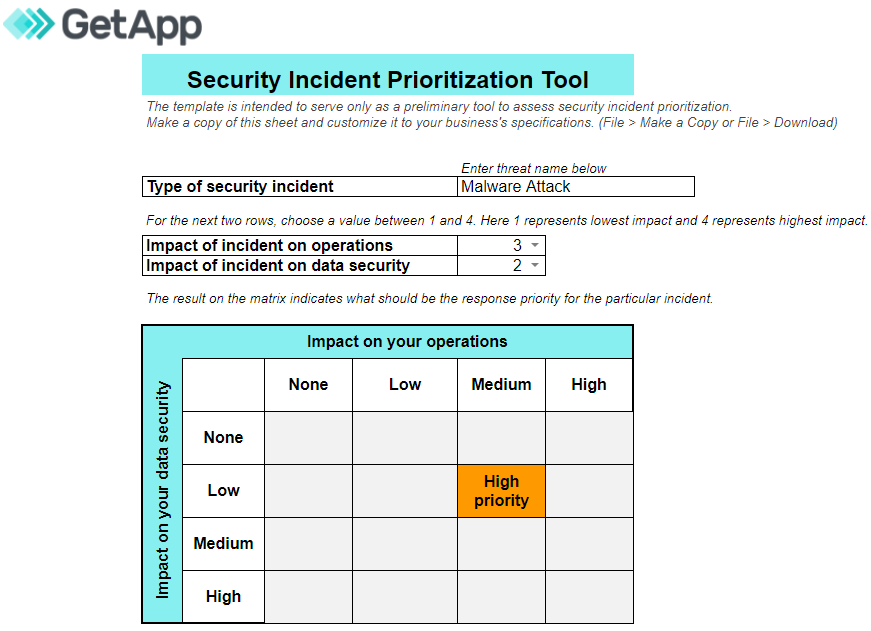
Use our security incident prioritization tool for the risk assessment of different security incidents. Mention how your operations and data are impacted (none, low, mid, or high), and the tool will automatically display if you should handle the incident on priority.
Also, set a time frame for resolving all identified incidents. High-priority incidents should ideally be resolved within two to six hours of detection, whereas low-priority incidents can be resolved within 24 hours.
3. Create an incident response flowchart with the steps to follow
An incident response plan will define the steps you should take to contain an attack. Have your plan in the form of a flowchart, so your incident response team members can quickly understand the threat mitigation path they need to follow.
Here’s a sample incident response flowchart.
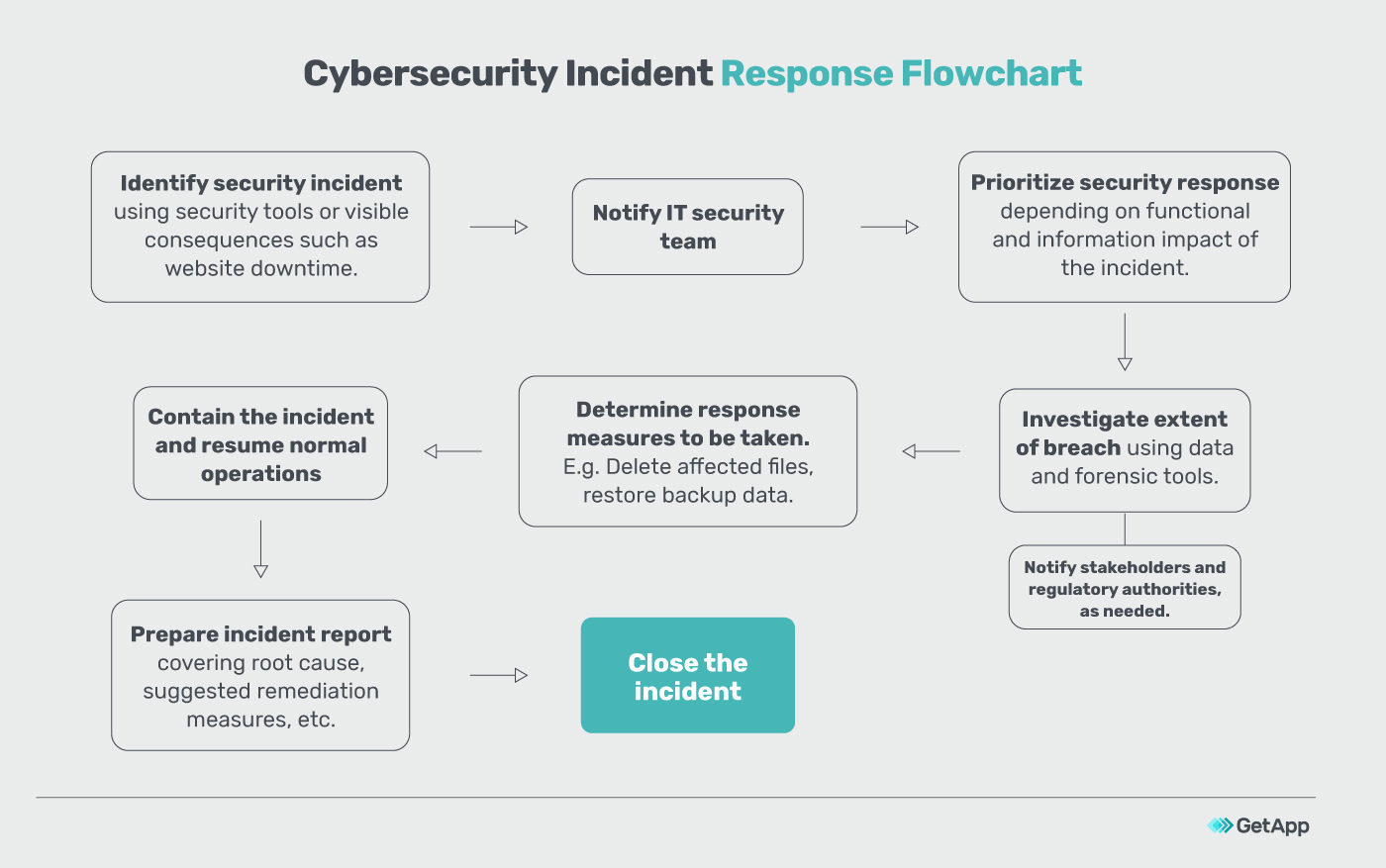
Also, outline who’s responsible for completing each step mentioned on your incident response flowchart. Assign clear, non-conflicting responsibilities to your staff members, so there are no clashes or conflicts.
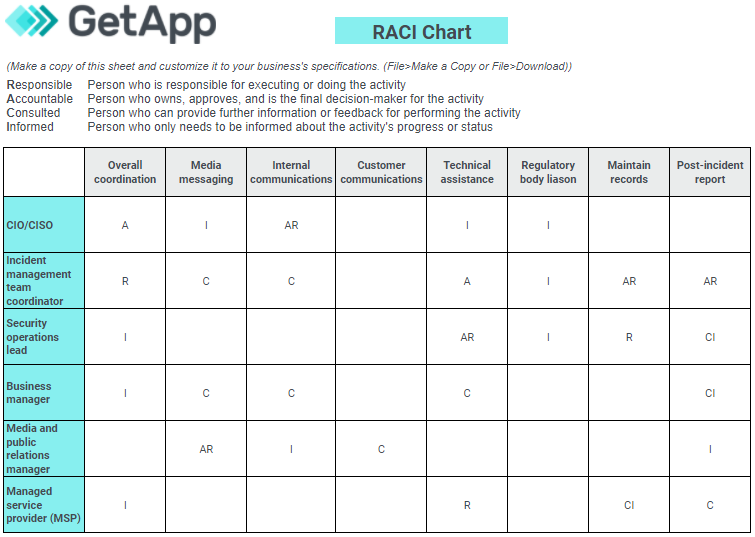
Use a responsible, accountable, consulted, and informed (RACI) chart to indicate who should be responsible for, accountable for, consulted on, or only informed about the different incident response steps. For example, your security manager will be responsible for maintaining incident records, accountable for technical operations, consulted on the preparation of the post-incident report, and informed about the overall coordination and liaison with regulatory authorities.
Here’s a sample RACI chart outlining the responsibilities of different members. You can download and customize the template per your needs. For example, if you don’t have an MSSP, your security manager will be the person responsible for all technical operations.
4. Conduct mock-ups and train your staff
Having an incident response program alone isn’t enough. You need to test its effectiveness by conducting mock drills, which will also train and educate your employees about their role in security incident management. Here’s a red-team vs. blue-team exercise you can conduct as a mock-up.
Red-team vs. blue-team exercise to test your organization’s incident response planning
Red-team vs. blue-team exercise is a cybersecurity mock drill modeled after military training courses. Your employees are split into two teams: red and blue. The red team tries to attack and break the blue team’s cyber defense, and the blue team tries to defend its internal networks and protect its systems and data.
The drill is conducted for a certain time period, say two hours, during which the red team uses various attack methods such as phishing, card cloning, and SQL scripting to exploit the blue team’s vulnerabilities and gain access to its systems. When the blue team detects an attack, it responds according to the steps mentioned in your incident response plan. You get an idea of how much time the response steps take and how effective they are. The exercise also lets you test the strength of your company’s current security posture.
5. Update your incident response plan regularly
Use the information collected from previous security incidents and mock drills to identify improvement opportunities and implement new controls for your security incident response plan (e.g., look for steps that can be automated).
Also, update your plan regularly to keep up with the changes in the threat landscape or to include details of any new security measures you’ve recently adopted. Revisit your response steps at least annually, and work on reducing the time you take to contain and recover from incidents.
Conclusion: Use security software to improve your incident response
Software tools can help you detect and mitigate security threats more effectively. They let you carry on with business operations even as incident response steps continue in the background. Here’s a list of some software tools you can consider using to improve your organization’s cybersecurity posture:
Want to know more about cybersecurity? Check out:

Gitanjali Maria