
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
How to Get PCI Compliant: The Process To Follow and the Tools You'll Need
PCI DSS compliance rules help protect payment cardholder data, improve customer trust, and strengthen security. This article helps understand how to get compliant.

Eighty percent of U.S. consumers prefer paying their bills with a debit or credit card, according to a study from payment processing provider TSYS.
This means: If you don't offer card payment options, you could be losing four out of five potential customers.
But, despite their preference for card payments, 6 out of 10 consumers are concerned about the security of their financial data when paying with a card at outlets such as gas stations and convenience stores, according to another study from ACI Worldwide.
This means that, not only must you offer card payment processing options, you must ensure that you do it securely. A major step in that direction and toward establishing security trust with your customers is becoming compliant with the Payment Card Industry Data Security Standards (PCI DSS).
What is PCI compliance?
PCI compliance refers to the set of technical and operational measures businesses must follow to ensure that the credit or debit card data of customers is protected.
The standard was created by the four major card issuing brands (Visa, MasterCard, Discover, and American Express) in 2004 to curb rising credit card fraud and establish security standards.
Who needs to be PCI compliant? All businesses that process, store, or transmit credit, debit, or cash card details need to follow the compliance rules, regardless of size or volume of transactions. You could be a merchant handling the payments or a third-party service provider, such as a payment gateway, handling card storage and processing.
Why is PCI DSS compliance important? While PCI compliance is not federally mandated, any event of a data breach due to non-compliance can lead to fines from the card issuing companies or your acquiring bank. The fines can range from $5,000 to $100,000 per month, which can break small companies. And, a breach of this kind will severely affect the reputation any business, large or small.
PCI compliance requirements often overlap with other regulations such as GDPR, meaning compliance with PCI DSS can help you meet other regulations as well.
(Source)
How to be PCI compliant—4 steps to take
Below we list the steps you'll need to complete to be PCI compliant.
1. Determine your compliance regulation level
Based on the number of transactions you process each month, PCI compliance regulations bracket your business under different levels. Identify which of the below levels your business belongs to. The security standards that you need to meet will depend on which level you fall under.
Level 1: Visa, Discover, or Mastercard: 6 million+ transactions. American Express: 2.5 million+ transactions
Level 2: Visa, Discover, or Mastercard: 1 to 6 million transactions. American Express: 50,000 to 2.5 million transactions
Level 3: Visa, Discover, or Mastercard: 20,000 to 1 million transactions. American Express: Fewer than 50,000 transactions
Level 4: All businesses processing fewer than the above-stated transaction volumes.
Businesses managing small transaction volumes need to complete only the self-assessment form for PCI validation. Companies handling large transaction volumes (Level 1) will need to be assessed by an external qualified security assessor (QSA) for confirming validation of PCI compliance.
2. Fill out the self-assessment form
Self-assessment questionnaires (SAQ) help you self-evaluate compliance with PCI DSS. There are nine different SAQ forms available on the PCI security standards website. You only need to fill out the one relevant to your business. For example, if you are an e-commerce firm, you need to fill out either type-A or type A-EP.
Self-assessment questions are bracketed under six broad headers, each of which tests whether you fulfill 12 key requirements:
I. Build and maintain a secure network
1. Install and maintain firewalls to protect data
2. Don't use default system passwords and other security parameters provided by the vendor
II. Protect cardholder data
3. Protect stored cardholder data
4. Encrypt cardholder data when transmitted across open, public networks
III. Maintain a vulnerability management program
5. Protect all systems against malware by regularly updating anti-virus solutions
6. Develop and maintain secure applications and systems
IV. Implement strong access control measures
7. Restrict access to cardholder data
8. Identify and authenticate access to systems
9. Restrict physical access to cardholder data
V. Regularly monitor and test networks
10. Track access to cardholder data and all network resources
11. Regularly test security systems and processes
VI. Maintain an information security policy
12. Maintain an information security policy
Each of the 12 requirements has additional sub-requirements or questions to help you identify security gaps in your payment process. You may also need to employ the services of approved scanning vendors (ASVs) to conduct vulnerability scans and penetration tests to assess your security systems.
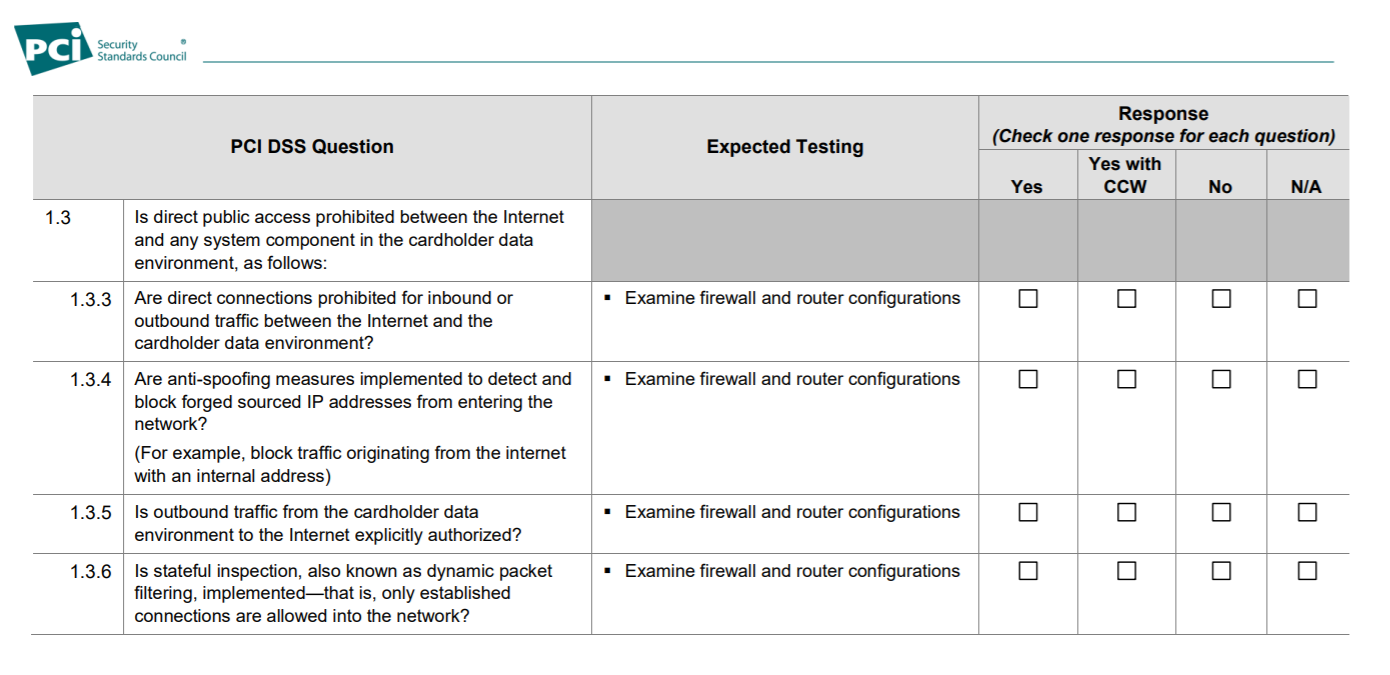
Questions from SAQ on firewall installation (Source)
3. Complete attestation of compliance (AOC)
After answering the SAQ, you need to complete the AOC to validate that you've complied with all applicable steps.
The form helps you to attest whether you're fully or partially compliant with the PCI DSS requirements. You'll need to improve security processes for the requirements you mark "partial" or "none" to obtain the PCI compliance certificate.
The AOC, along with the system and organization control (SOC) report and other documents such as ASV scan reports need to be submitted to your respective acquirer bank and card issuing brand.
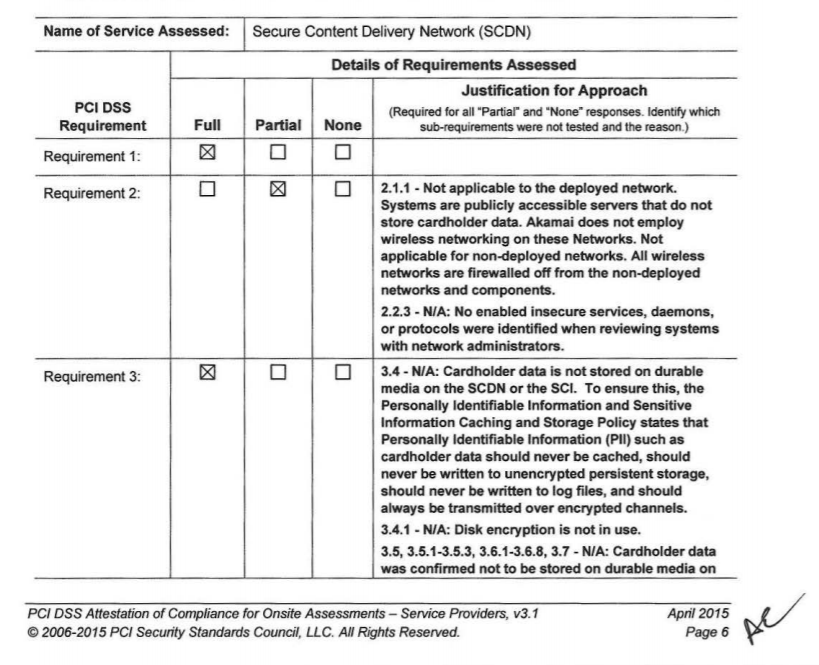
Screenshot from an AOC document (Source)
4. Get your PCI compliance certificate
In addition to the above steps that validate whether you're PCI compliant, your business will be assessed and audited by a QSA, or qualified security assessor. On successful verification and validation of your controls by the QSA (which can take up to six months) you get the PCI certificate.
The PCI compliance certificate is valid for one year from the date of issue. To maintain compliance, you need to complete the SAQ annually and conduct quarterly network scans.
How to be PCI compliant—Technology that helps
Technology solutions can help you meet the PCI requirements. Many of the PCI DSS requirements explicitly talk about implementation of software solutions to safeguard card data.
Here, we look at software solutions that can help you comply with PCI standards.
Firewalls: A network security tool that controls incoming and outgoing network traffic and establishes a barrier between trusted and untrusted traffic. PCI DSS requirement No. 1 focuses on implementing a strong firewall configuration.
Tokenization: Helps protect cardholder data (requirement No. 3) by replacing sensitive data with tokens. Tokenization ensures that merchants will never see the actual card numbers, but only a string of tokens.
Encryption: Encryption tools help you mask card data and other sensitive information when stored or transmitted. Requirement No. 4 of PCI DSS requires you to encrypt credit card data stored in your database as well as in-transit, using techniques such as AES.
Anti-virus/anti-malware: PCI compliance requirement No. 5 mandates that you always have an updated antivirus or anti-malware solution to detect and quarantine threats. New-gen antivirus solutions use predictive analytics to gather threat intelligence and prevent attacks.
Access controls: Access control tools allow you to restrict access to cardholder data using techniques such as privileged accounts and role-based access. Requirement No. 7 of PCI DSS refers to providing users only the minimum required access to data.
Authentication: Authentication tools help you verify and validate the identity of the person seeking access to cardholder data. It keeps unauthorized persons from accessing data and is a part of requirement No. 8.
Security information and event management (SIEM): SIEM software helps you log security information and events that can be analyzed to determine security threats. The software supports continuous network monitoring and periodic audit information review. These tools help you meet requirement No. 10 and some elements of requirement No. 11.
Vulnerability management: Vulnerability management tools help you comply with requirement No. 11 and support vulnerability scanning, intrusion detection, file integrity monitoring, and penetration testing. Often, vulnerability management tools also provide anti-malware capabilities.
Check out the list of PCI compliance software that offers broad overall credit card data protection by providing multiple features such as SIEM, vulnerability management, anti-malware protection, reporting, and incident response plan.
If your security expertise is limited, we recommend that you partner with a managed security service provider (MSSP).
Interested in learning more about security?
Visit our IT Security directory for all your IT security software needs.

Gitanjali Maria

