
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
5 Tips To Maintain Security When Employees Work Remotely
Remote work offers flexibility to employees but introduces security challenges for employers. Get tips to mitigate security risks if you have remote employees at your small business.

Remote work has offered employees the flexibility of location—they can work right from the comfort of their homes or from a nearby cafe. For businesses, however, this practice has introduced a new challenge: maintaining security for remote workers.
According to our 2022 Data Security Survey*, insufficient remote access security is one of the top three IT security vulnerabilities businesses face. In another survey**, 15% of SMB leaders say remote desktop vulnerability is the main reason for ransomware attacks on their business.
In this article, we discuss five Gartner-backed tips[1] to help security leaders at small businesses develop a security strategy that not only offers remote work protection but also ensures a smooth working experience for employees. We’ve also provided our free security assessment template, which businesses can use to identify potential risks, evaluate existing security controls, and implement new ones.
Tip #1. Develop a comprehensive remote work security policy
With the shift to remote and hybrid work, employees are no longer confined to secure office spaces. They could be working from homes, coffee shops, airports, or coworking spaces—all of which have unsecured Wi-Fi networks. Thus, it's essential for your small business to have a security policy that specifically addresses such remote work circumstances.
This policy will serve as a roadmap for employees to follow when working remotely, helping them navigate potential cybersecurity risks. It should include guidelines on secure internet connections, virtual private network (VPN) usage, and device management, among other practices, to ensure your sensitive company data remains protected.
Here are a few things to keep in mind when crafting your remote work security policy:
Involve key stakeholders from your organization. Ideal candidates are people from HR, legal, compliance, and IT. They’ll help ensure your policy is robust as well as practically feasible.
Be prudent with rules. Only establish rules you can genuinely enforce. For example, instead of requiring a specific antivirus product in all employee devices, just mandate antivirus use.
Keep the policy up to date. Revisit your security policy every six months or so to ensure it reflects changes in technology, business operations, emerging threats, etc.
Prioritize clarity. Draft your policy in simple language. For instance, instead of using technical jargon such as “Utilize VPN for encrypted communication,” simply say “Always turn on your VPN.”
Remote work comes with its unique set of challenges—unsecured networks, phishing scams, and the overlap of personal and work spaces to name a few. These risks make remote employees vulnerable to cyberthreats, and that's where security awareness training can help. It equips your team to navigate security challenges when working remotely.
Follow these best practices when designing a security training program for your remote workforce:
Break down risky behavior. Explain to your team the pitfalls of risky online habits such as clicking links in unsolicited emails or connecting to public Wi-Fi networks.
Stay ahead of attackers. Keep your team updated on the latest cyberthreats. Use team communication tools such as Slack and Microsoft Teams to regularly share newsletters on recent security events/incidents or tips on safe online habits.
Use your remote work policy as a guide. Update your remote work security policy (discussed in the last section) with topics such as “handling sensitive data remotely” and “remote work risks” to guide and educate your employees.
Use free resources if budget is a constraint. Organizations such as the National Institute of Standards and Technology (NIST)[2] provide free security awareness training materials. These resources not only save costs but also provide your team with expert, trustworthy information.
Tip #3. Prioritize physical security
Physical security is a critical but often overlooked aspect of remote working. Even simple factors such as where an employee’s computer is positioned or how they store documents can have considerable security implications. For small businesses, ensuring physical security is even more crucial, as they typically lack dedicated IT teams to manage security breaches.
Implement these measures to boost physical security for your remote workforce:
Install privacy screens. These are excellent tools for preventing unintended information sharing, especially when working in public spaces. They restrict the computer screen view to only the person sitting directly in front, shielding your business data from curious onlookers.
Use shredders. Remote employees working with sensitive information on paper documents should always have a shredder handy. It’s a simple and effective tool to dispose of sensitive documents and prevent information leaks through discarded documents.
Get secure document storage. Your remote work policy should have clear instructions on secure physical document storage. If secure storage isn’t possible at an employee’s location, advise them to completely avoid using physical documents.
Assess home setup locations. Guide your employees to set up their workstations away from windows and other public areas in their homes. Also, recommend keeping voice-activated devices such as Alexa or Google Nest away from the workstation to avoid accidental eavesdropping.
Tip #4. Rethink workstation configurations
Secure remote work also involves reconfiguring employee workstations and fine-tuning rules for USB storage, personal devices (BYOD), and remote printing. Each could potentially be a gateway for security breaches if not managed correctly.
USB storage guidelines
USB devices, though handy, can pose significant security risks, such as introducing malware or acting as gateways for data extraction. Here are a couple of ways your small business can limit these risks:
Disable USB access. Block automatic syncing on mass storage devices such as thumb drives and smartphones to prevent unauthorized data transfers. You can implement this by adjusting your device settings or using security software.
Control USB permissions. Deny access to nonessential USB-connected hardware by limiting read, write, and execute permissions. You can allow access to necessary peripheral devices such as keyboard, mouse, and webcam while limiting other hardware access to secure employee workstations.
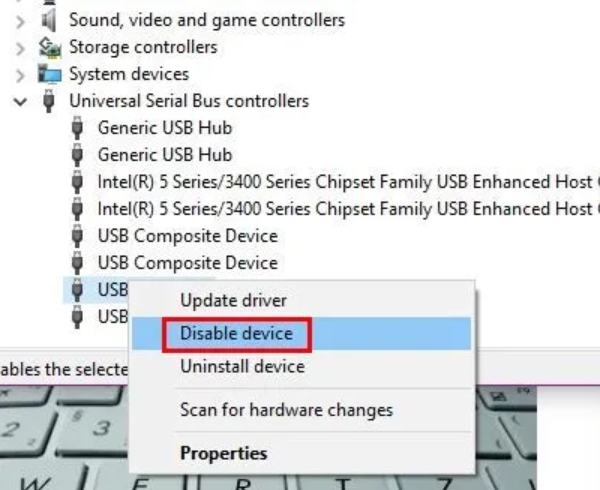
Microsoft’s device manager settings to disable USB ports in Windows devices[3]
Bring your own device (BYOD) guidelines
Allowing remote workers to use their personal devices for work can save costs for your small business, but it also introduces unique security challenges. Here are some ways to keep the remote BYOD work culture safe:
Adopt zero trust network access. The zero-trust policy operates on the fundamental belief that no user or device should be trusted by default. Each remote access request, therefore, should be verified. Adopt solutions that support this strategy, including cloud-based services and authentication mechanisms such as multi-factor authentication (MFA).
Use secure coding practices. Use business applications that are developed using secure coding standards such as W3C and ECMA. These security standards help prevent, detect, and eliminate coding errors that could compromise security in the software tools and apps your business uses.
Adopt a risk-based approach. Group remote employees by the sensitivity of the applications or data they access. For high-risk cases, for instance, you could mandate the use of virtual desktop infrastructure and remote control software. For low-risk employees, on the other hand, browser headers and cookies could be used for simple device identification.
Remote printing guidelines
Remote printing, while convenient, can expose your business data to risks such as interception during transmission or physical theft of printed documents. Here’s how to manage these risks:
Control remote printing. Restrict it only to those remote workers who absolutely need it. This practice will minimize the chances of data exposure during transmission.
Offer alternatives. If printing risks are high, provide alternatives such as PDF editing tools to mitigate the need to print and thus reduce risks such as loss or theft of printed documents.
Tip #5. Use data loss prevention software
Data loss prevention (DLP) software is a great tool to protect your data from falling into the wrong hands. It's like a virtual vault that secures your business’s confidential data when your employees are working remotely. Let’s discuss the different types of DLP solutions and how you can use them to handle remote working challenges:
Enterprise DLP (EDLP): EDLP is similar to a central surveillance system that oversees data safety policies across your business, including remote work. For instance, if you’re a small retailer with an online and physical presence, EDLP can help manage data safety for both channels—retail card transactions and online customer data.
Integrated DLP (IDLP): IDLP can integrate into the business tools your remote employees already use, such as your email system or web gateway, to flag data protection risks in existing processes. For example, if you use an email service, an IDLP solution can identify and flag sensitive information such as credit card details in the emails employees send.
Cloud-focused DLP: With remote work, the use of cloud-based apps and storage has increased. Cloud-based DLP solutions are designed to secure data in these environments. If your remote team relies on cloud storage for customer records or other sensitive data, a cloud-focused DLP solution can ensure your data remains secure and accessible only to authorized personnel.
Assess your remote work security posture
Maintaining remote work security isn’t a one-and-done deal. It’s about understanding where you stand and then taking steps to tighten the locks, and our free security assessment template allows you to do just that. Scroll to the end of this article to download the free template.
Use it to evaluate the strength of your small business’s current security posture by identifying areas for improvement and addressing them with the tips we’ve shared above. You can also check out our comprehensive cybersecurity guide to equip your small business with the right security tools.
Sources
1. 5 Tips To Protect Data for Remote Workers, Gartner
2. A Handbook on Computer Security, Employee Awareness, and Training, NIST
3. Restrict USB Devices, Microsoft
Methodology
*GetApp’s 2022 Data Security Survey survey was conducted in August 2022 among 1,006 respondents who reported full-time employment. 289 respondents identified as their company’s IT security manager. The goal of this survey was to gauge the general state of cybersecurity at U.S. businesses and understand the use of various data protection controls.
**GetApp’s 2022 Ransomware Impacts Survey was conducted in May 2022 among 300 U.S. business leaders that have experienced a ransomware attack. All respondents were part of the response team or were made fully aware of the company’s response. The goal of this survey was to determine the wider impacts of ransomware attacks on businesses (i.e., repercussions beyond the ransom payment.)

Bhavya Aggarwal

