
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
Here's What Ransomware Victims Say Hits Hardest—And It's Not the Ransom
A new era of ransomware brings multifaceted extortion, productivity loss, and lost revenue. Learn why one in three companies that don’t pay a ransom still incur total costs above $50,000.

Ransomware attacks have been growing in number and severity for years, with headlines typically focused on ransom demands that have climbed to amounts once unthinkable. As a result, you might be concerned about your company’s ability to pay a ransom if attacked.
But our research finds that ransom payments make up only a fraction of a ransomware attack’s full impact—in fact, our survey finds that, among companies that have paid a ransom, only 11% say the ransom payment was the most consequential impact of the ransomware attack.
In this piece, we’ll examine the results of our 2022 Ransomware Impacts Survey (see methodology below), identify the impacts victims find most consequential, and provide tips on how to protect yourself against attacks.
Multifaceted extortion is becoming the norm—and it’s nearly twice as effective
We surveyed 300 ransomware victims to understand more about the wider consequences of these increasingly severe attacks and found that three in five (60%) victim companies suffered a multifaceted extortion attack. This means that not only were the victim’s files encrypted, but a separate attack was also launched to add pressure and force them to the bargaining table (or sometimes to obscure the deployment of malware in advance of the ransomware attack).
This typically happens in the form of data theft and/or a distributed denial of service (DDoS) attack—and this strategy of adding insult to injury is quite literally paying off for attackers.
Our data shows that 58% of multifaceted extortion victims pay the ransom compared to only 31% of standard ransomware attack victims. That means the success rate of multifaceted extortion is nearly double that of traditional ransomware attacks.
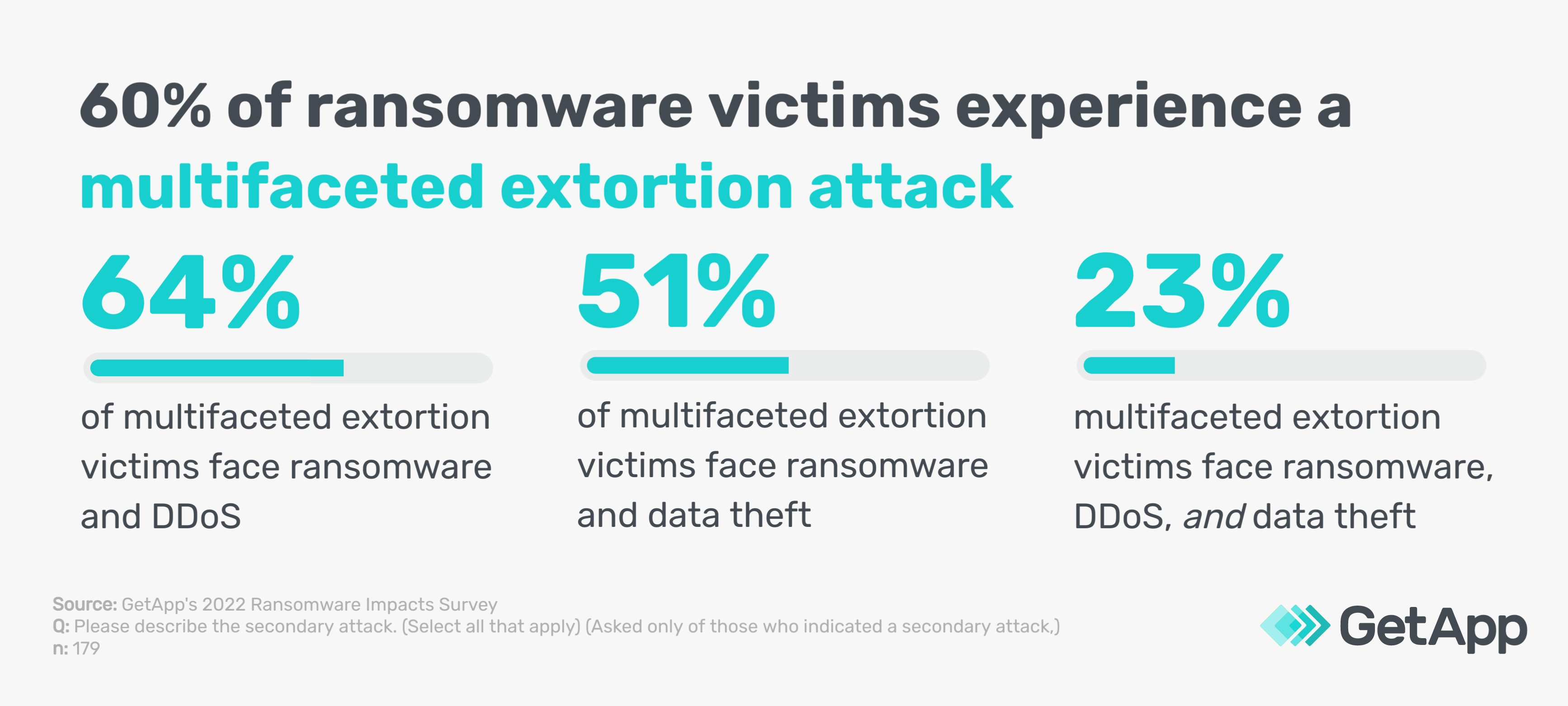
In a DDoS attack, the victim's servers are overloaded with web traffic, making their website inaccessible to clients. Sixty-four percent of the multifaceted extortion victims in our survey experienced both a ransomware attack and a DDoS attack.
Another common add-on attack involves data theft, whereby the ransomware gang accesses the victims’ systems in advance, exfiltrates a copy of the data, and threatens to leak it online. In other words, ransomware gangs are effectively threatening a data breach at best and to compromise sensitive customer data or trade secrets at worst. Among the multifaceted extortion victims in our survey, 31% grappled with data theft alongside a ransomware attack.
Nearly one in four (23%) of the multifaceted extortion victims in our survey experienced a triple extortion event comprising a ransomware attack, a DDoS attack, and data theft.
Multifaceted extortion attacks demand the full-attention of your IT team, prevent customers from accessing your website, and risk data breaches that could result in regulatory fines or damage to your company’s reputation. It’s only a matter of time until additional forms of extortion take hold.
Recommended reading: How to Prevent a DDoS Attack—6 Strategies for Small Businesses
Productivity loss viewed as most significant impact
Productivity losses were selected as the single most consequential impact of a ransomware attack by 37% of victims, more than any other option. Productivity also appears to be a key pressure point when it comes to paying the ransom. Among companies that paid the ransom, a full 70% reported that the attack made a major impact on productivity, compared to only 40% of companies that did not pay the ransom.
Below is the full breakdown of companies that opted to pay the ransom.
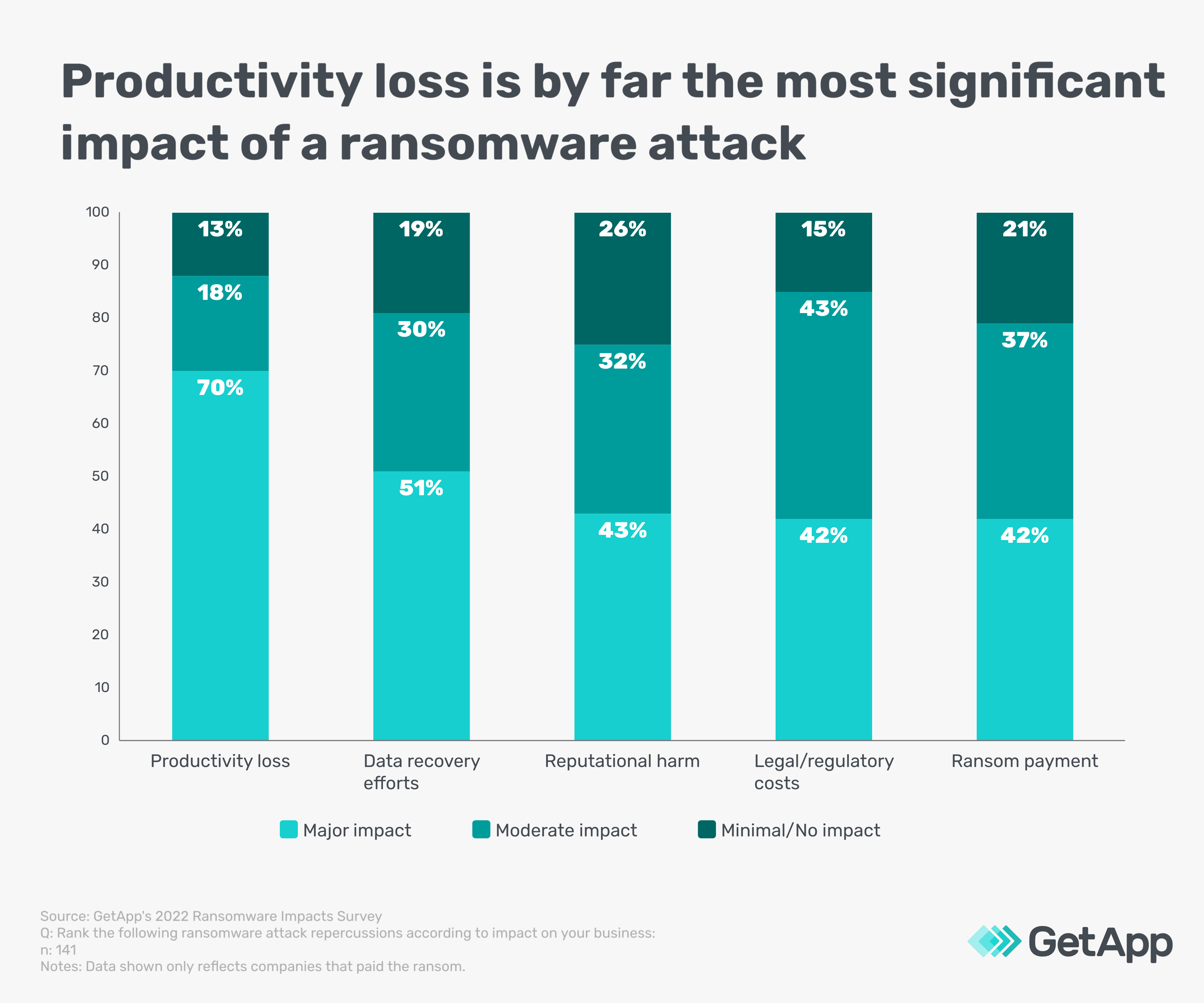
Despite being the attack’s namesake, the ransom payment itself sits among reputational harm and legal/regulatory costs in overall significance and well behind productivity losses and data recovery efforts.
83% of ransomware victims lost revenue—and 62% lost clients
Only 17% of our respondents said that their company did not lose revenue as a result of the attack. This makes sense. Not a lot of businesses can make money while employees are without access to internal systems or data for an extended period of time.
Our research finds that only 31% of ransomware victims had their operations back up and running within six hours of an attack. Another 42% had their systems operational within 24 hours, but an alarming 27% of ransomware attacks lasted for days, including 8% of attacks that went on for a week or longer.
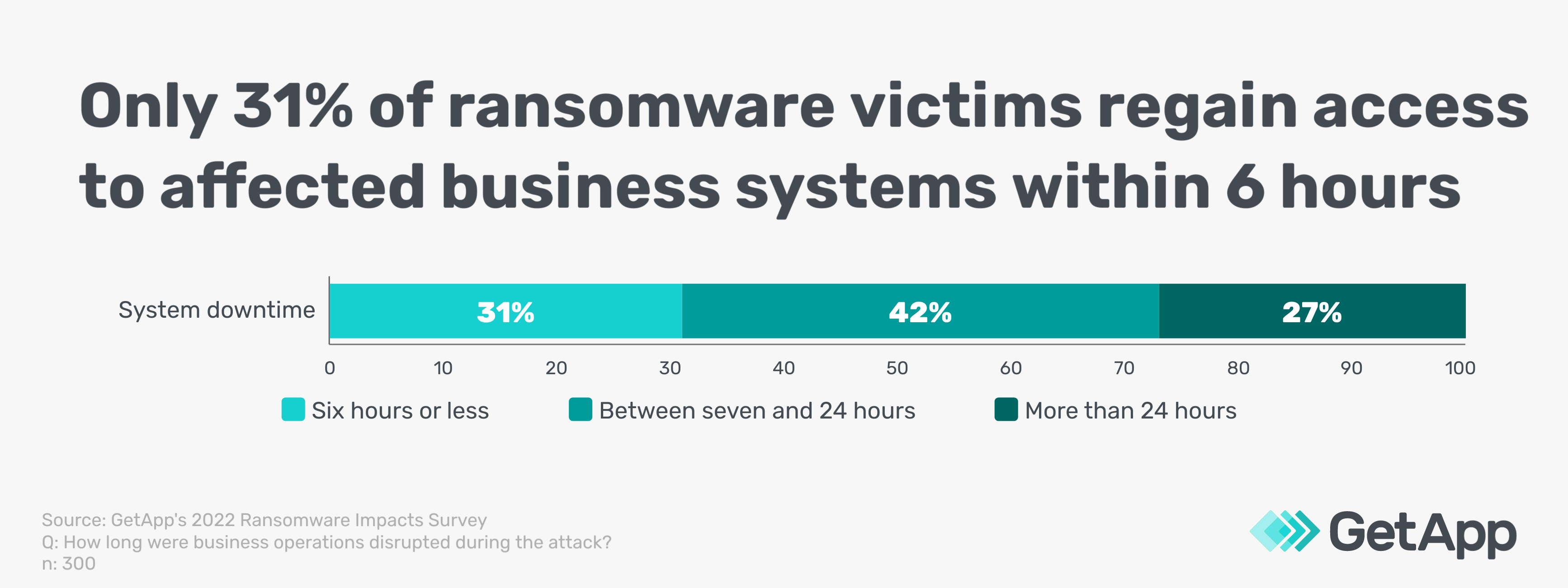
Clearly, productivity losses and downtime play a significant role in lost revenue, but at least these issues are temporary. Losing a client, on the other hand, is often permanent.
More than three in five (62%) ransomware victims report losing a client due to a ransomware attack—38% report losing multiple clients. This isn’t surprising considering the reputational fallout companies face when a major ransomware attack hits the news, along with factors such as websites being down, inaccessible points of contact, and missed deadlines.
Even companies that don’t pay a ransom experience heavy financial impacts
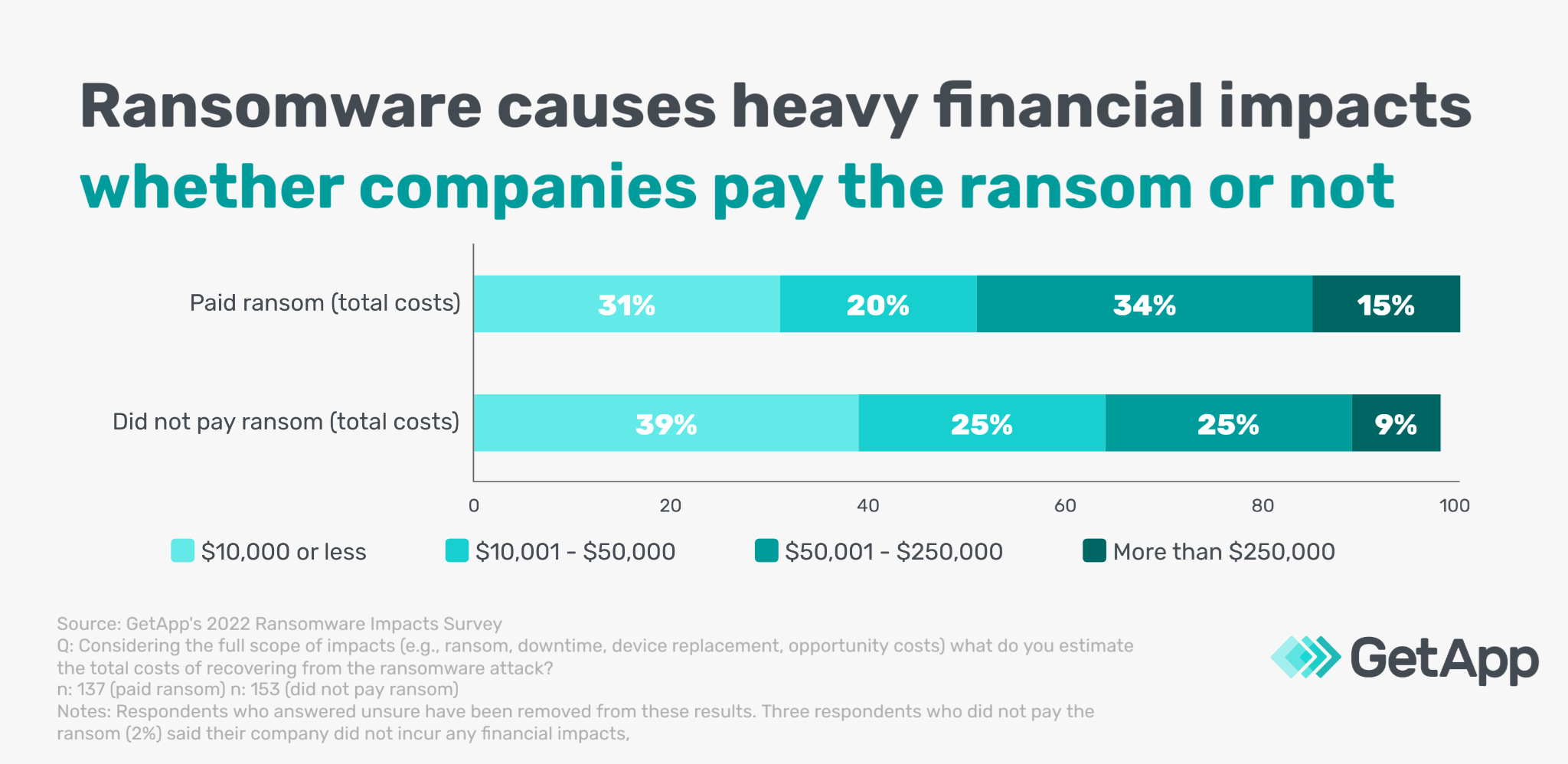
We asked respondents to estimate the total financial impact of the attack, including everything from downtime to device replacement (and the ransom payment, if applicable). Forty-nine percent of companies that paid a ransom report impacts of more than $50,000.
But one in three (34%) companies that did not pay a ransom still incurred total costs above $50,000 and nearly one in 10 (9%) incurred impacts totalling more than a quarter million dollars. So while the ransom certainly tends to result in a higher overall cost, it’s only a portion of the total impact.
Ultimately, it’s best to prepare for an attack, not a payment
No business is safe from ransomware attacks. That’s why it’s important to take some basic precautions to guard against the primary methods ransomware gangs use to infiltrate your network, including phishing emails, software vulnerabilities, and remote desktop protocol (RDP) compromise.
Protect against phishing emails
Phishing schemes remain a premier threat to your company’s security and according to our data security report, they’ve never been more effective. Ensure your staff is trained on how to detect phishing emails and consider using phishing tests to gauge their susceptibility. To help, we’ve developed the following resource: How to Spot Phishing Emails—A Brief Guide
Ensure all systems are patched
Many ransomware variants take advantage of software vulnerabilities to either enter a system or move within it. Make sure all software is up-to-date and discontinue using any end-of-life software or devices that no longer receive updates. Don’t forget about IoT devices that are often difficult or impossible to patch—host these devices on a separate network.
Secure remote connections
Remote desktop protocol (RDP) compromise is a top target for ransomware attacks on Windows-based systems. Enable automatic updates from Microsoft, change the default port from 3389, and always follow password policy best practices to prevent brute-force attacks on RDP-enabled machines. Similarly, your company must be diligent about the use of virtual private networks (VPNs) and other networking equipment that have become popular targets for ransomware gangs.
Develop a plan to minimize business disruption
A full 95% of ransomware victims created or updated a cybersecurity incident response plan following an attack. Instead of waiting for an attack, be proactive by making sure you have an up-to-date incident response plan in place ahead of time. But don’t stop there. Make sure you also have a business continuity plan in place to minimize costly disruption during a cyberattack. This includes avoiding a ransomware attack’s worst outcome (i.e., total data loss) by ensuring all company data is continually backed up (and that the backups are safe).
To learn more, review our guide to creating a cybersecurity response plan, check out our anatomy of a business continuity plan infographic, and visit our business continuity software catalog to find the best solution for your company.
Methodology
GetApp’s 2022 Ransomware Impacts Survey was conducted in May 2022 among 300 U.S. business leaders that have experienced a ransomware attack. All respondents were part of the response team or made fully aware of the company's response.


