
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
How to Prevent a DDoS Attack—6 Strategies for Small Businesses
DDoS attacks are becoming stronger and more complex. We’ll help you understand the threat and offer strategies to help protect your business.

Distributed denial of service (DDoS) attacks threaten to bring down your website and leave your business offline for hours or even days on end. And once a DDoS attack has ended, picking up the pieces is a long and costly process.
DDoS attacks have grown more powerful and complex over the years, and they spare no website or network. Small businesses are often more vulnerable than large enterprises because they lack the IT resources to detect and mitigate a DDoS attack. Our recent survey of small-business owners found that 75% of them are concerned about DDoS attacks.

You can read our business model survey methodology at the bottom of this page
But, even with limited resources, small businesses can—and should—implement a strategy for safeguarding against DDoS attacks, using a combination of cloud infrastructure and network monitoring.
In this article, we’ll explain the concepts you need to understand about DDoS attacks and show you some ways to avoid becoming a target.
Targeted by zombies: How a DDoS attack works
In DDoS attacks, multiple (distributed) systems flood a server, website, or other network resource with connect requests, messages, or other communication packets. The goal is to slow the system down, crash it, or make it otherwise inaccessible.
The concentrated attack and subsequent system shutdown results in a “denial of service” for legitimate users.
First, an attacker creates a so-called “DDoS master” by exploiting vulnerabilities in a remote computer. The compromised system then targets multiple computer systems and gains control of them using malware. The systems under the control of the attacker are known as its “zombies.”
The attacker then uses the traffic generated by the compromised devices to flood the target domain and shut it down.
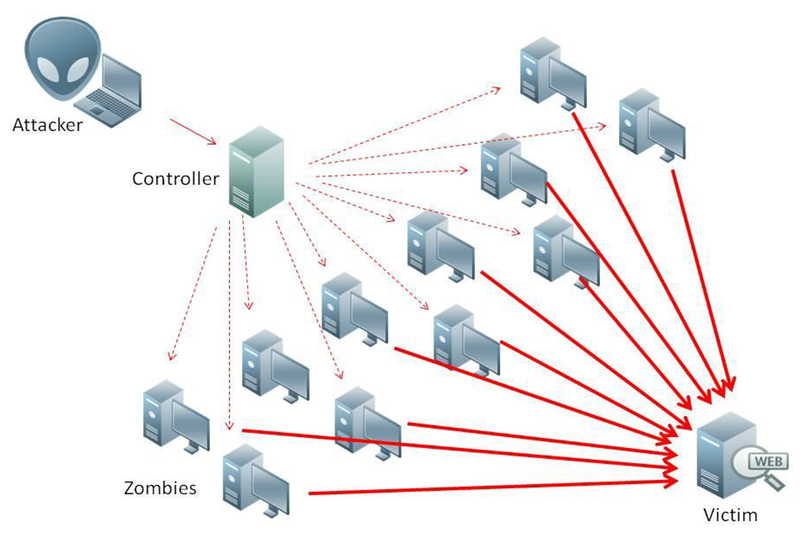
DDoS attacks are distributed because they use many zombies to increase attack strength and complexity (Source)
DDoS attacks are growing stronger while becoming easier to carry out
DDoS attacks are simple to orchestrate and relatively inexpensive to carry out. Manual methods of launching a DDoS attack are now being replaced by automated programs capable of more complex and persistent attacks. Today, DDoS attacks can be carried out as a service on the dark web by renting out botnets for as little as $10 per hour.
Botnet: A network of internet-connected devices infected and controlled as a group by a common type of malware, without the owners’ knowledge.
The strength of a DDoS attack is often measured in megabits per second (Mbps) or gigabytes per second (Gbps), but as they grow in strength more and more attacks are being measured in terabytes per second (Tbps).
Withstanding volumetric attacks becomes difficult, especially for small businesses, as you need extra bandwidth to absorb the surge in traffic. And the volume of bandwidth needed to absorb all of that network traffic is expected to increase as DDoS botnets incorporate more mobile endpoints and internet of things (IoT) devices.
IoT botnets fuel bigger DDoS attacks
Poorly secured devices—such as smart cameras, thermostats, or other personal devices—are easy targets for attackers to launch malware-based DDoS botnets. These attacks are large—300 Gbps or more—and more difficult to prevent.
Between 2016 and 2018, the Mirai botnet gained remote access to millions of vulnerable IoT devices, bringing down countless websites with massive DDoS attacks. Popular security blog KrebsOnSecurity came under sustained DDoS attack from more than 175,000 IoT devices.
Few companies are able to withstand DDoS attacks. Most crash for a few hours or days, and some even permanently.
In 2016 the servers of Dyn (a company that controls most of the U.S.' DNS servers) suffered sustained DDoS attacks, bringing down prominent websites including Twitter, Netflix, Reddit, and CNN. The Mirai botnet (which carried out the attack) had over 100,000 zombies and a strength of 1.2 Tbps.
In 2018 GitHub faced 1.35 Tbps of prolonged traffic, going down for 10 minutes. It was able to mitigate the sustained DDoS attacks by routing traffic through DDoS mitigation provider Akamai Prolexic’s larger network.
In February 2020 Amazon Web Services (AWS) was hit by the largest DDoS attack ever recorded with a volume of 2.3 Tbps. The event was 44% larger than any other volumetric attack on AWS.
In October 2020 Google revealed for the first time that their infrastructure had “absorbed a 2.5 Tbps DDoS in September 2017, the culmination of a six month campaign that utilized multiple methods of attack,” which would retroactively make it the largest ever DDoS attack.
Domain Name System (DNS) is the internet’s system for converting alphabetic names in a web URL into number IP addresses.
But volumetric attacks aren't the only DDoS tactic. Application layer attacks can cause just as much damage with less bandwidth by targeting application vulnerabilities. Additionally, protocol attacks focus on using up a server’s resources rather than overwhelming it with traffic.
DDoS aftermath: Downtime, financial losses, and compounding vulnerabilities
A Kaspersky survey found that 30% of businesses do not take any preventive measures, because they believe they are unlikely targets for DDoS attacks. This closely aligns with our own findings that 25% of small-business owners are not concerned about DDoS attacks.
DDoS attacks are often used as a diversionary tactic intended to leave your system vulnerable to other cyberattacks. While you’re distracted, the attacker might actually be injecting malware or stealing valuable data.
System downtime resulting from DDoS attacks affects your business operations and your customers’ ability to reach you, causing a reduction of services and a failure to process customer transactions.
DDoS attacks also cause financial damage. Businesses incur costs not only to fight a DDoS attack, but also recovery costs (such as paying overtime for engineering resources to restore services). Lost revenue and business opportunities only add to the damage.
6 ways to prevent a DDoS attack
While preventing a DDoS attack may not always be possible, there are many ways to detect them and mitigate their impact before they get out of hand.
1. Use cloud services to take advantage of your service provider’s bandwidth resources
One way to minimize the impact of DDoS attacks is by over provisioning bandwidth.
Using cloud-based software is a simple and cost-effective option for small businesses. Cloud computing supports bandwidth pooling and resource autoscaling, making cloud customers more resilient to DDoS attacks. Cloud-based services are scalable, and you can take advantage of the service provider’s resources to deal with DDoS attacks.
Internet service providers (ISPs) can help with additional bandwidth when needed. Work with your ISP to learn what mitigation services they provide in the event of a DDoS attack, but don't rely on them or your cloud services provider exclusively. If you do, you could end up being the collateral damage of an attack on either provider.
To plan for this, monitor your network continuously to detect abnormal traffic and work with your ISP to reroute traffic or block attacks inline as soon as they are detected.
2. Detect traffic anomalies with network monitoring and DDoS mitigation tools
Small businesses must monitor bandwidth and remain alert to potential traffic spikes that could indicate a DDoS attack or virus. Network monitoring tools help monitor traffic and alert you whenever there is an unreasonable spike, providing a first level of security. These tools, along with DDoS mitigation tools, help to detect and mitigate DDoS attacks.
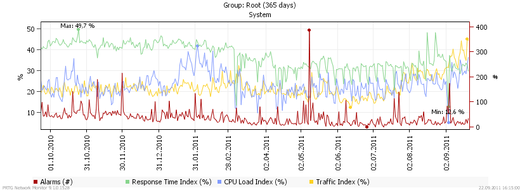
Network monitoring graphs in security software platform Paessler (Source)
Analyzing your network logs will alert you to security threats on your network. Network firewalls, load balancers, and web application firewalls are other tools that help strengthen your network defenses. DDoS mitigation service providers, such as Akamai or Arbor Networks, reroute the excess traffic to a mitigation center and scrub it, allowing only legitimate traffic to reach your website.
3. Update security elements to mitigate cybercrimes aided by DDoS attacks
Since DDoS attacks cover up for a variety of other cybercrimes, you need to install and update your other security tools, such as anti-virus software, advanced threat detection systems, and security patches.
Updated security features reduce the damage that an attack can cause, including financial theft, data theft, or ransomware. Unpatched servers and application vulnerabilities are easy targets for hackers. You must ensure that any open source platforms you use (such as WordPress) are updated as soon as updates are available, and security flaws are fixed.
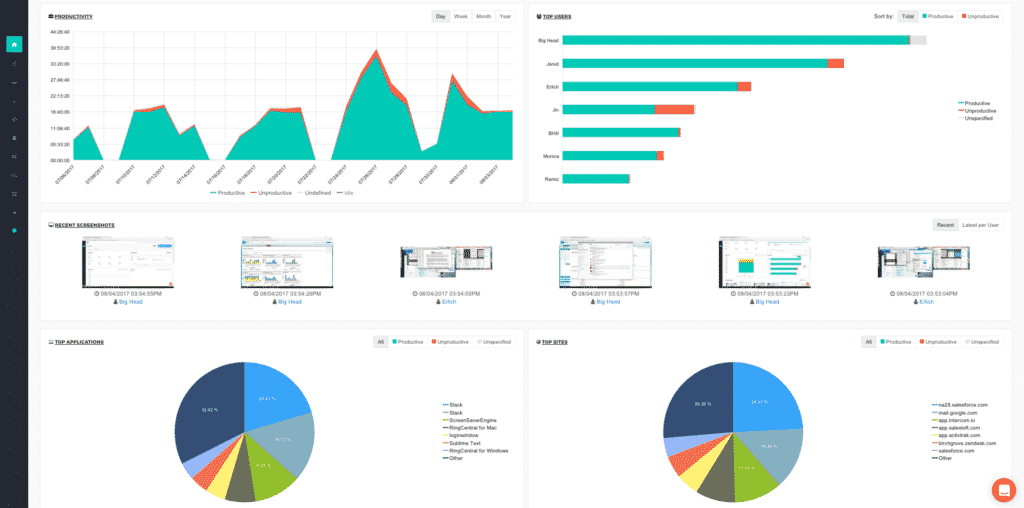
Anti-virus solution ActivTrak (Source)
4. Develop a DDoS mitigation action plan before it’s too late
There is little you can do to stop an attack once your website or server is already under a traffic assault besides go into emergency mode.
One way to be prepared in advance, however, is to keep an action plan ready that your business will follow in case of a DDoS attack. This should include the emergency contact details of your ISP, members within your business who need to be notified, and incident report templates that explain what's happening.
5. Safeguard your website with Google’s Project Shield (if applicable)
Project Shield is Google’s free service that helps protect websites from DDoS attacks. It displays cached content to website visitors, which reduces traffic requests to your web server and absorbs potential DDoS attacks. The project supports only news, election monitoring, human rights, and individual journalism' websites (after review of an application).
6. Consult a security expert to implement DDoS prevention techniques
If you feel you’re not equipped to handle IT security on your own, look for security experts who can advise you on DDoS prevention techniques and more.
If you decide to engage a DDoS mitigation company or other type of security vendor, check out their client base, past experience, and support options before finalizing a deal.
Visit our cybersecurity software catalog to find the tools you need to protect your network from all types of attacks.
Additional updates by Zach Capers, Senior Content Analyst
Methodology and Disclaimer
The business model survey referenced in this article was conducted by GetApp from June 18 to June 23, 2020 among 577 respondents who reported executive leadership roles at small businesses with 500 or fewer employees.
Note: The applications selected in this article are examples to show a feature in context and are not intended as endorsements or recommendations. They have been obtained from sources believed to be reliable at the time of publication.

Gitanjali Maria

