
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
A Security Director Explains 9 Types of Penetration Testing for SMBs
Shut down the hidden pathways for hackers by understanding different types of pentesting.

Not all types of penetration testing are suitable for every situation. That's something Colleen Morrissey [1], acting director of information security at Rensselaer Polytechnic Institute, wants small-business IT managers to remember when planning a penetration test to uncover hidden hacker entry points in their operations.
Morrissey believes that in order to avoid unanticipated system disruptions during the test, it's crucial to choose the right pentesting type. She suggests your pentesting strategy should align with your business objectives, compliance and insurance requirements, risk appetite, and financial budget. It's also crucial to define the scope and limits of the test with all stakeholders involved.

Colleen Morrissey, Acting director of information security at RPI
This will all help you to select the right pentesting type and approach for your business, so you don’t end up wasting your time and resources.
What is penetration testing?
Penetration testing is a cybersecurity exercise where your IT team brings in ethical hackers to break into your business's IT security infrastructure. Using manual and automated processes, these “white hat” hackers aim to breach specific areas you request, such as applications, the cloud, or online networks.
This proactive approach allows them to identify weak spots and vulnerabilities that unscrupulous hackers could exploit, potentially causing havoc within your business operations. Once these weak points are uncovered, penetration testers don't just leave your team hanging—they help your IT staff understand the impact of these security gaps being exploited and patch them up using various security and compliance software tools.
For a more comprehensive approach, penetration testing can be performed using three main techniques.
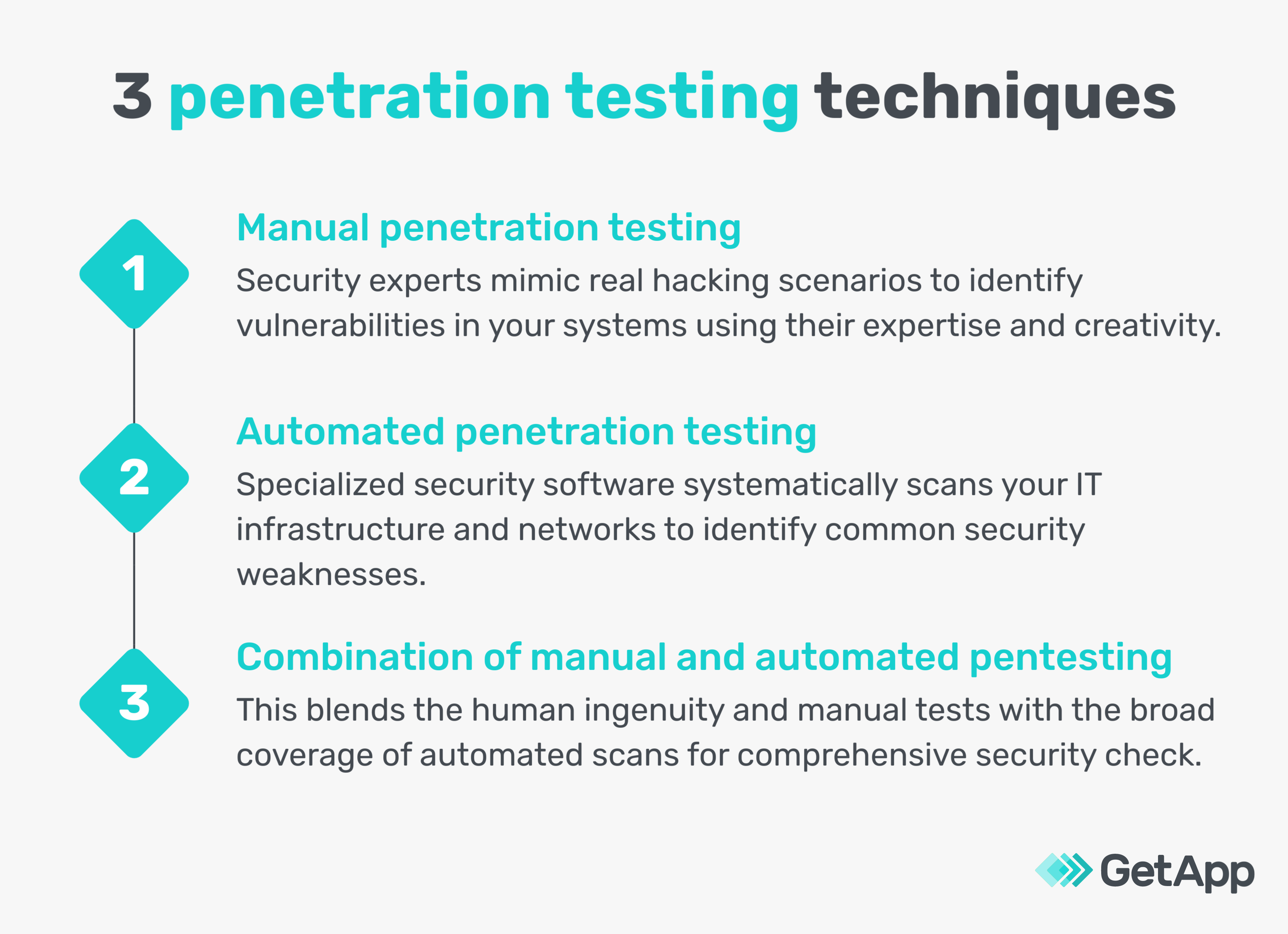
In addition to these three techniques, there are nine different types of penetration testing your small business can conduct to uncover anomalies.
9 pentesting types to scan different areas of your small business
Morrissey addresses the need to figure out which type of pentesting will work best for your business by saying, “businesses should adopt a risk-based approach to security, choosing the type of penetration testing that aligns with their unique threats. For instance, a public-facing app might warrant an application-specific pentest, while a closed IT perimeter with potential insider threats could call for an internal network pentest with social engineering.”
1. External network penetration testing
Imagine a potential hacker lurking outside your business searching for a way in. That's precisely what an external network penetration test tries to simulate. It's all about finding those tiny cracks in your defenses—perhaps outdated software or an unnoticed open port—that could invite trouble such as phishing and DDoS attacks.
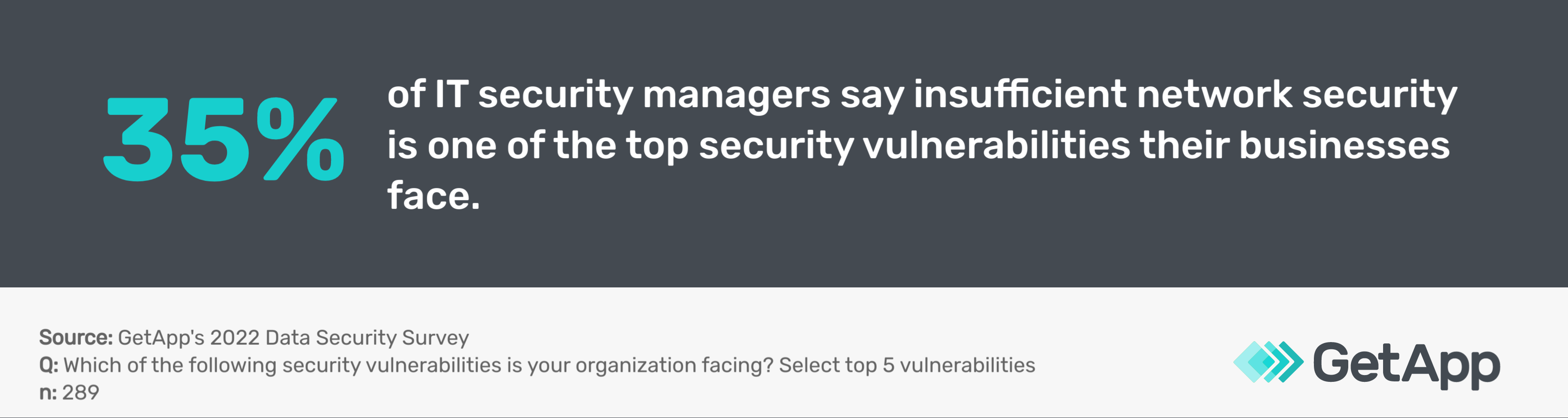
However, one significant challenge is the constant need to stay updated with the latest threats. As Morrissey advises, it's crucial to test your perimeter defenses regularly. They're your first line of defense against external threats. Firewalls, fraud detection, and other network security systems must be updated and properly configured. This type of testing should be a priority, especially for businesses with a significant online presence, such as eCommerce platforms.
2. Internal network penetration testing
Now, let's switch gears and think about an insider threat—perhaps a disgruntled employee. An internal network penetration test checks things from within your network, primarily focusing on access controls. The real challenge here is ensuring robust security without hindering your business's speed.
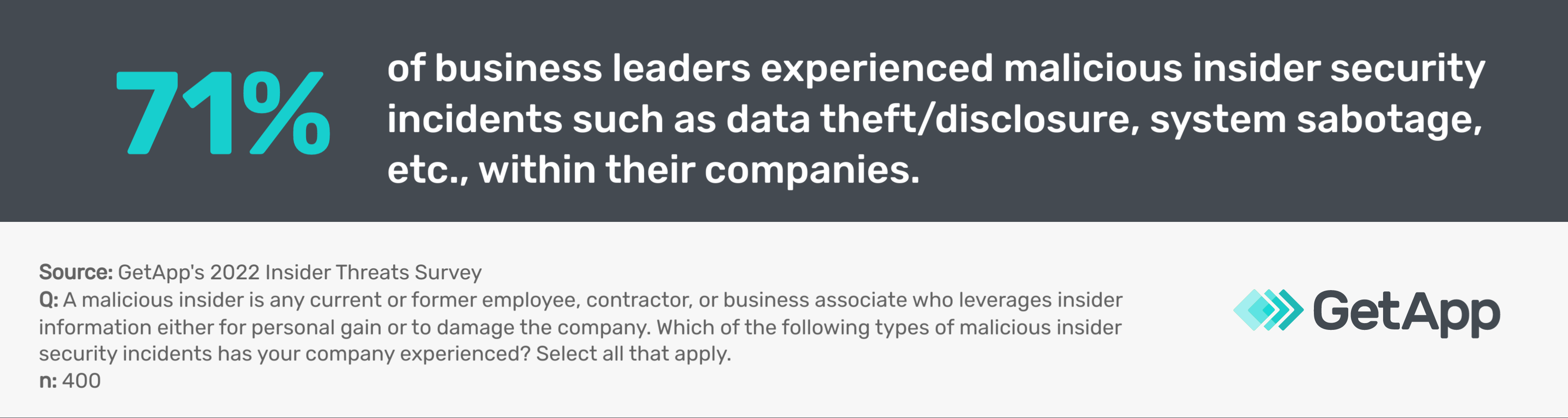
Morrissey suggests that while external threats are serious, the potential for internal threats shouldn't be overlooked. Regularly audit your internal access controls. Make sure employees only have access to the systems they need. A careless or disgruntled employee can cause just as much damage as an external hacker. As your business and employee base grows, you’ll need to become more mindful of this.
3. Wireless penetration testing
A wireless penetration test ensures that your wireless networks aren’t an easy path into your system for hackers by checking encryption standards and scanning for rogue access points. The aim here is to ward off eavesdropping and man-in-the-middle attacks. The real challenge lies in keeping the network and mobile devices secure without making it difficult for legitimate users to access.
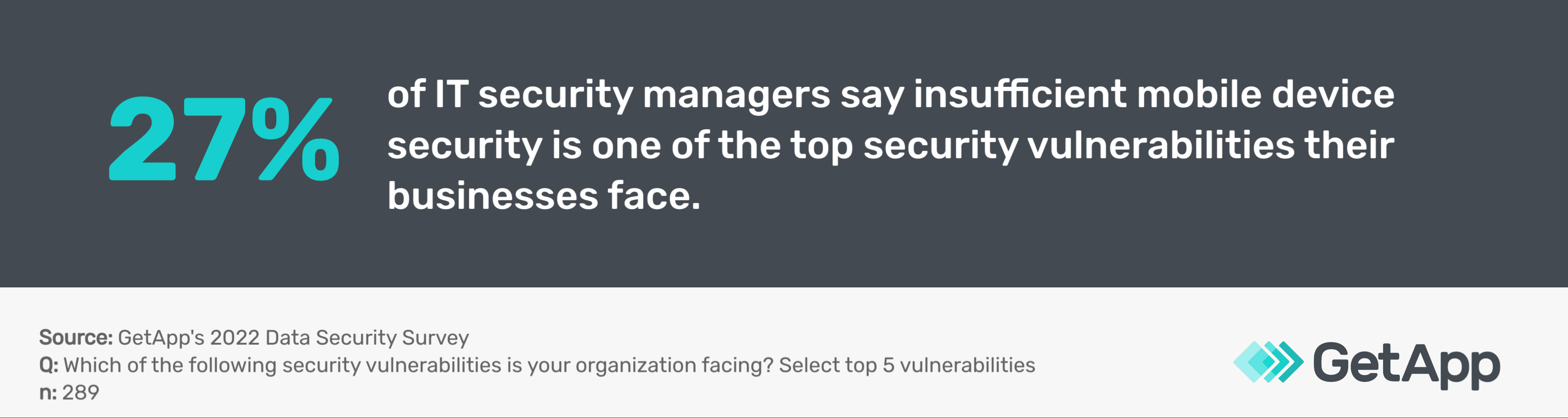
As Morrissey points out, wireless networks can be an easy entry point for hackers if not properly secured. Businesses that provide free Wi-Fi to customers or use wireless networks extensively, such as cafes or retailers, should ensure they have strong encryption and regularly check for rogue access points. A good practice is to keep your business and guest networks separate to minimize risk.
4. Physical penetration testing
Physical security isn't just about traditional locks and guards; in today's tech-driven world, it intersects seamlessly with digital. Physical penetration testing assesses your tangible assets, including how well-integrated digital security mechanisms protect your premises.
Morrissey believes it's not just about keeping intruders out; it's about managing who gets in. While robust doors and alert guards are essential for physical security, the digital security component can't be ignored. Secure access points with card swipes or biometric systems ensure that only authorized individuals gain entry.
Employing multi-factor authentication at critical access junctures, using security cameras wisely, and having efficient visitor management systems solidify your defense. Especially for businesses like manufacturers or retail outlets, blending traditional and tech-driven security is the way forward.
5. Social engineering penetration testing
Have you ever received a suspicious phone call or email? Social engineering penetration testing ensures your staff knows how to spot these. It's all about preventing unauthorized access and data leaks that could be caused by human error. The challenge is to foster awareness without creating a culture of fear.

Morrissey advises that employees are your first and last defense against social engineering attacks. Regular training can help them recognize and respond appropriately to phishing emails, suspicious phone calls, and other social engineering tactics. It's important to remember that security is as much about people as technology. Companies with customer-facing roles, such as call centers or customer service departments, should be especially vigilant about this type of testing.
6. Application penetration testing
Application penetration testing checks your software for weaknesses that could lead to attacks such as SQL injection. The main hurdle is ensuring that security is maintained throughout development.
According to Morrissey, applications are often the gateway to your sensitive data. Regularly test and update your applications to ensure they are secure. If you're developing your applications, incorporate security from the design phase. Building security from the start is much easier and cheaper than fixing problems later. Tech companies and businesses that develop their own software or apps should prioritize this type of testing.
7. Cloud penetration testing
Your data's not always in your hands when it comes to the cloud. Cloud penetration testing ensures that your cloud-based assets are locked down tight to prevent unauthorized remote access and data breaches. The tricky part? Understanding the shared responsibility of security in the cloud.

Morrissey advises that cloud environments offer great advantages but have unique security challenges. It's crucial to understand your cloud provider's security measures and what responsibilities fall on you. Always encrypt sensitive data in the cloud and use strong, unique passwords for all cloud accounts. This should be a focus area if you're a business heavily relying on cloud services, like many startups and tech companies.
8. Internet of Things (IoT) penetration testing
Smart devices are convenient, but they can also be a hacker's dream. IoT penetration testing checks these devices for weaknesses to thwart potential attacks. The biggest challenge with this is dealing with the enormous variety of IoT devices.
Morrissey points out that IoT devices often lack the security measures of traditional IT systems, making them attractive targets for hackers. Make sure to update your IoT devices and change any default passwords regularly. Put IoT devices on a separate network to minimize potential damage if compromised. Businesses that use a lot of smart devices should pay close attention to this.
9. Blockchain penetration testing
It's new, it's exciting, but blockchain needs to be tested too. Blockchain penetration testing checks for weaknesses in your networks and smart contracts to prevent possible attacks. The difficulty here is dealing with a new and constantly evolving technology.
Because blockchain technology is so new, it comes with unique security challenges. Regularly audit your blockchain networks and smart contracts for vulnerabilities. Be wary of “security through obscurity”—just because something is new or complex doesn't mean it's secure. Businesses that deal with cryptocurrencies or use blockchain technology, such as fintech companies, should prioritize this type of testing.
3 approaches to conducting penetration testing
There are three approaches to carrying out these penetration tests: Black Box testing, White Box testing, and Grey Box testing. Knowing them helps you pick the right strategy that aligns with your business's unique needs and circumstances.
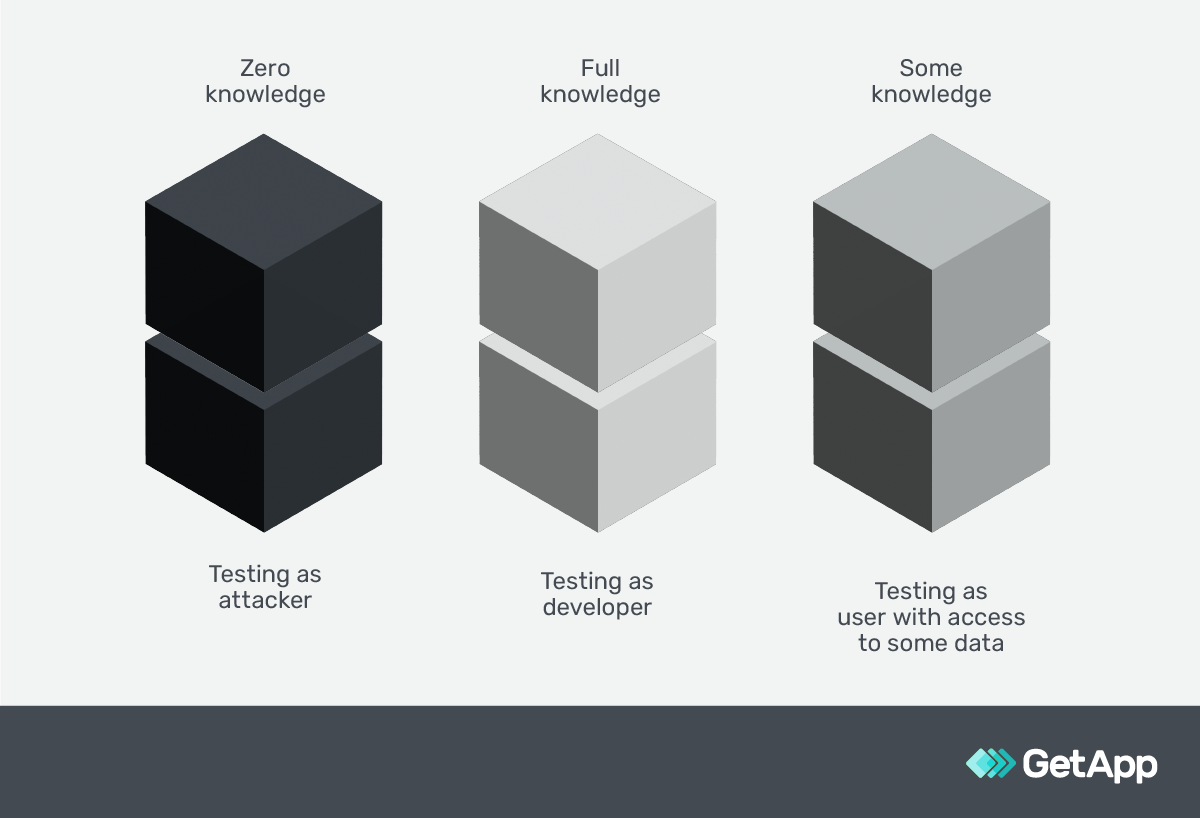
Diagrammatic representation of three pentesting approaches
Black Box testing
In this "mystery" approach, you don't provide prior knowledge about your company's IT environment, such as network structures or firewalls. Ethical hackers are in the same position as real-world attackers, trying to figure out external vulnerabilities such as outdated software or open ports. Morrissey notes this approach gives a realistic understanding of potential external threats but could overlook internal threats such as rogue employees. Also, due to the lack of initial information, it's time-consuming and can be costly.
Important note
Morrissey adds that there's a specialized subtype of Black Box testing known as a “double-blind” penetration test. In this approach, most of your employees remain unaware of the test. It allows you to accurately assess how your internal team would respond in a genuine security incident scenario.
White Box testing
Contrary to the Black Box approach, you provide complete access to your IT infrastructure, including system configurations, source code, and network protocols. This allows ethical hackers to conduct a thorough analysis, leaving no stone unturned. Morrissey points out that this approach allows for a detailed analysis of your system but demands high-level access and cooperation from your IT team.
Grey Box testing
This approach is a balanced blend of Black Box and White Box testing. You provide limited knowledge about your IT environment, such as network diagrams or system architecture, to ethical hackers. Morrissey suggests this approach strikes a balance between realism and thoroughness. The success of Grey Box testing depends mainly on the level of knowledge you provide to the testers.
What factors should small businesses consider when deciding the type of penetration testing?
Morrissey advises that your choice of penetration testing types and approaches will largely depend on these factors:

Morrissey adds, "In a perfect world, you'd perform all applicable tests using both Black Box and White Box approaches. However, due to resource and cost constraints, this isn't practical for most organizations. So, you'll need to prioritize according to these factors."
Penetration testing complements your broader security strategies
Penetration testing is an invaluable exercise as part of your company's cybersecurity discipline, but it's not a one-size-fits-all solution. Morrissey believes the key lies in selecting the correct type of testing that aligns with your business's needs.
She further adds that depending on your specific needs, any or all of these pentesting types can be combined. For instance, if you’re a SaaS provider leveraging current technology stacks, you might need network, wireless, physical, cloud, and application penetration testing to evaluate your environment. But if you have no IoT devices, there's no need for IoT penetration testing.
So, plan and conduct carefully. Familiarize yourself with your IT infrastructure and potential vulnerabilities first, then plan a pentest. Below, GetApp's security assessment template can help you evaluate the strength of your current security posture. Knowing where vulnerabilities can be exploited might give you a clearer idea of the type of penetration testing that will most benefit your small business.
Sources
Colleen Morrisey, LinkedIn

Bhavya Aggarwal

