
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
How To Mitigate The Different Types of Insider Threats in Cybersecurity
Insider attacks are often more dangerous and difficult to detect than external threats. Understanding the types of insider threats can help you prepare a strong insider threat mitigation plan.

If you suffer a security breach, there’s a good chance it will come from within your company. According to a Verizon report, one out of three data breach incidents involved insiders (your employees or partners) exposing confidential information.
Insider attacks stem from malicious intent or negligence of your associates. Compounding the problem, according to Gartner, nearly 60% of workplace misconduct goes unreported, giving malicious insiders an easy run.
To make matters even worse, when insiders are caught, the issue is often downplayed or handled internally to avoid the publicity that might result from prosecution.
In this article, we discuss the types of insider threats in cybersecurity, the damages it can cause, and how you can mitigate insider risk. We also speak with an expert in the field to understand how small businesses are affected by insider threats and what measures they can take against it.
What are insider threats in cybersecurity?
Insider threats in cybersecurity are a security risk wherein people within your organization (employees, contract workers, former employees, or other business partners) expose or delete confidential data or sabotage your critical IT assets, causing you revenue and reputation loss. Insider attacks involve people whom you trusted misusing their legitimate access privileges for personal gain or unwittingly exposing your business data.
Types of insider threats
Various types of insider threats exist in all businesses and being aware of them is important to help you take the necessary precautions.
1. Malicious insider
A malicious insider is somebody who takes advantage of their legitimate access to your data and IT systems to achieve personal gain through illicit means.
Malicious insider threats could be persons who associate with your business with malicious intent and may be incentivized in some way to commit the crime. It could also be a current or former employee taking proprietary data along with them to their next employer or to set up their own business.
Employees’ malicious intent can also stem from personal pressures in life (e.g. debt, addiction), or association with cyber criminals. Malicious employees often lack proper oversight and are in a position to both commit and conceal a misdeed.
2. Disgruntled employee
A subset of malicious insiders, the motivations of disgruntled employees stem from a need for retribution rather than personal gain. Employees who feel jilted in some way by the company, a superior, or co-worker might act with the intention of harming the company.
This might include sabotaging systems, exposing confidential data, or attempting to harm the company’s reputation. A well-known example of this occurred at Gillette when a disgruntled product engineer shared highly confidential designs for the company’s then proprietary three-blade razor with Schick (who immediately notified Gillette).
3. Negligent insider
A negligent insider is someone who unintentionally causes a security incident due to accidental data breach, misuse of systems, or downloading malware. And while the cause is sometimes laziness or lack of diligence, it’s often the case that a well-meaning negligent employee is simply unaware of the information security risks posed by the improper use of company applications or insecure devices.
Phishing: One of the most common baits used to trap inadvertent insiders
Phishing emails (spurious emails that look genuine but contain malicious links) continue to be one of the main ways cyber criminals target inadvertent insiders. Our data security survey finds that 58% of employees had clicked on a phishing email in 2020, which is 15% higher than in 2019. To combat phishing, employees should be encouraged to contact email senders via secondary means (e.g., direct message, walking over to their desk) to confirm unusual requests (e.g., “Did you just send an email asking me to send over everyone’s tax documents?”)
Train your employees on how to spot phishing emails
4. Vendors and contractors
Occupying a grey area in which outsiders become insiders, vendors and contractors are often the sources of insider threat activity. These insiders often have access to sensitive systems and regulated data that can be sold or compromised. And because these workers are not formally employed by your company, they do not always have the same allegiance to your company and might therefore be less vigilant about information security practices.
For example, the infamous Target data breach was the result of an HVAC contractor’s stolen credentials. In another instance, AT&T paid more than $25 million in fines for breaches that occurred at vendor call centers. Before handing system access over to a vendor or contractor, inquire about the security controls they have in place to protect your data.
The cost of insider attacks
Insider attacks cause organizations to lose nearly 5% of their revenue to occupational fraud each year, with the median loss per case estimated at $125,000, according to the Report to the Nations from the Association of Certified Fraud Examiners (ACFE). Accounting, sales, operations, and executive/upper management teams contributed to more than half of all the occupational fraud cases.
The report also finds that small businesses (less than 100 employees) lose more per insider attack (median loss of $150,000) compared to larger companies (median loss of $140,000). Small businesses are likely to feel the impact of this loss much more than their larger counterparts because of their revenue and resource constraints.
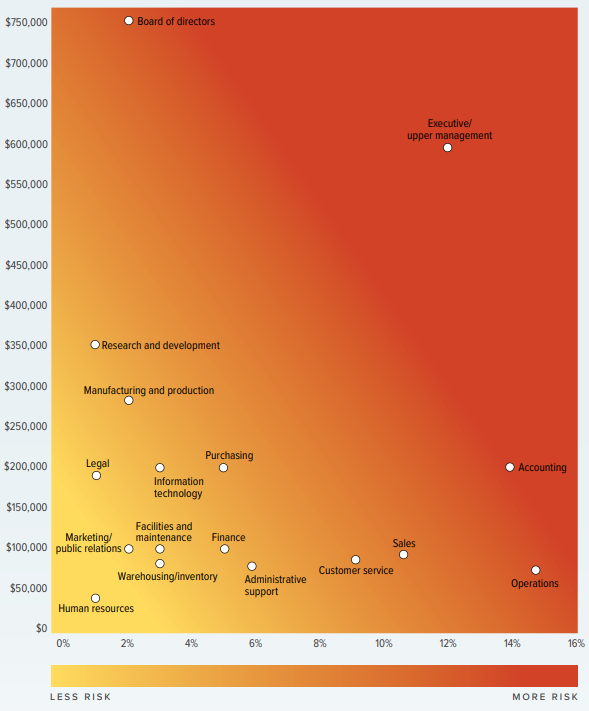
ACFE’s occupational fraud risk by department (Source)
Q&A with Andi McNeal, Director of Research for ACFE
To find out more, GetApp spoke with Andi McNeal, CFE, CPA, director of research for the Association of Certified Fraud Examiners (ACFE) to understand more about insider risks for small organizations. Here’re snippets from our chat.
GA: In what ways are small businesses more vulnerable to insider attacks than large companies?
AM: Small businesses have several aspects that make them particularly vulnerable to insider attacks. First, these companies typically do not have the resources to invest in sophisticated prevention and detection mechanisms that larger organizations do, which leaves them more susceptible to being victimized.
The smaller staff size compounds this challenge, as many duties that can be separated at larger organizations are performed by a single person at smaller companies, which gives that individual increased opportunity to both commit and conceal a fraud scheme.
Small companies also tend to run on trust more than larger organizations—that is, many small businesses have a familial culture, where everyone knows and trusts everyone else, so formal checks and balances often go unenforced. Finally, management at small businesses is more likely to underestimate the risk, either due to lack of technical knowledge about insider threats or to the common “it can’t happen here” mindset that many small-business owners or leaders hold.
GA: What measures can small businesses take to mitigate the threat of insider attacks?
AM: The most important measure small businesses can take is to educate all employees about how these schemes affect the company, its reputation, and its staff, and how it’s everyone’s job—not just IT’s—to help guard against these schemes.
Employees should not only be taught IT security best practices and how to perform their jobs to limit risk, but they should also be encouraged to watch for warning signs that the company has been or could be victimized—from observing suspicious behavior to identifying a weakness in the system that could be exploited—and provided with specific information on how to report such concerns.
Due diligence and background checks during the hiring process can also help small businesses make sure they’re not inviting a known thief in through the front door.
GA: How can software or technology be used to detect occupational fraud?
AM: Our research shows that the use of software to proactively monitor and analyze data for anomalies is one of the most effective ways to combat fraud. In the Report to the Nations, organizations that used proactive data monitoring and analysis caught schemes more than twice as fast and experienced frauds that were 56% smaller than organizations that did not use a similar approach.
And while implementing an analytics program can involve investing in expensive software tools and needing highly-trained staff to write sophisticated queries, there are also numerous analytics techniques to help identify occupational fraud that can be run in Excel or other low-cost solutions.
Other technology controls that can be used to help prevent and detect employee fraud schemes include automating the enforcement of a strong employee password policy and restricting and/or monitoring employee access to systems and accounts.
Mitigating all types of insider threats
Recognizing that trusted employees might pose a threat is not something that most business leaders want to confront. That’s why most companies focus primarily on external threats while preferring to ignore insider threats.
Unfortunately, ignoring insider threat indicators doesn’t make them go away. Instead, you need a strong insider threat program—measures designed and enforced to detect and mitigate insider risk. Here are some elements to include in your insider threat program.
1. Improve internal controls
Practice multi-factor authenticationfor system access.
Enforce segregation of duties and dual control processes to make offenses more difficult to commit and cover-up.
Require that employees use all of their vacation time (insider schemes are often discovered by the person covering the role of the vacationing offender).
Classify data into distinct categories and restrict access according to the role.
Ensure that sensitive data is encrypted.
Regularly perform internal audits and log reviews.
2. Use software to monitor data
Employ data loss prevention (DLP) software to monitor activity and data transmissions.
Choose an endpoint protection platform (EPP) that controls ports and can restrict access to devices such as USB drives.
Apply behavioral analytics to discern activities that are out of the ordinary.
Employ sentiment analysis, a form of data mining, to gauge employee feelings toward the company.
Use a cloud access security broker (CASB) to monitor and restrict data transmission to the cloud.
3. Cultivate a culture of integrity and security awareness
Provide reporting options such as an anonymous hotline or a formal whistleblower program.
Adopt a comprehensive security policy (include AUP, BYOD, and data classification policies) to define how data, apps, and devices may and may not be used.
Establish proper "tone at the top" by ensuring that upper management maintains and displays high ethical standards.
Design dedicated insider threat awareness training.
Explain why certain actions negatively affect the company, rather than simply telling employees not to do things.
Ultimately, there is no simple solution to insider threats. Notice the title of the article mentions mitigating insider threats not preventing them. That’s because locks keep out only honest people. Dishonest people just kick your door in, take your stuff, and sell it.
You need to trust your employees and allow them the freedom to access a variety of data to do their jobs without feeling oppressed or micromanaged. Improving internal controls, fostering an ethical company culture, and educating employees about how their actions might inadvertently harm the company can reduce all types of insider threats.
You may also like to read:
Methodology
GetApp’s 2020 Data Security Survey was conducted from September 10 to September 11 among 868 respondents who reported full-time employment. Of the 868 respondents, 267 identified as IT professionals and 83 identified as their organization’s IT security manager.
(Additional updates by Gitanjali Maria, Senior Specialist Analyst)


