GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
Building A 5-Phase Cybersecurity Lifecycle Framework for Your Business
Cybersecurity investments can lose direction if there is no proper framework to guide them.

Whether you’re a small, midsize, or large business, a cyber attack can be extremely costly and even fatal to your business’s survival. An example is the ransomware attack on an Arkansas-based telemarketing firm that reportedly had to shut down operations and lay off 300 employees.
To avoid a similar catastrophe, you should build a security program that can help your teams proactively identify and respond to cyber threats. To do that, you can refer to the National Institute of Standards Technology (NIST) framework, which according to Gartner is used by 73% of organizations worldwide (full content available to clients only).
In this article, we’ll explain how to create a 5-phase cybersecurity lifecycle framework that can holistically improve your organization’s security posture.
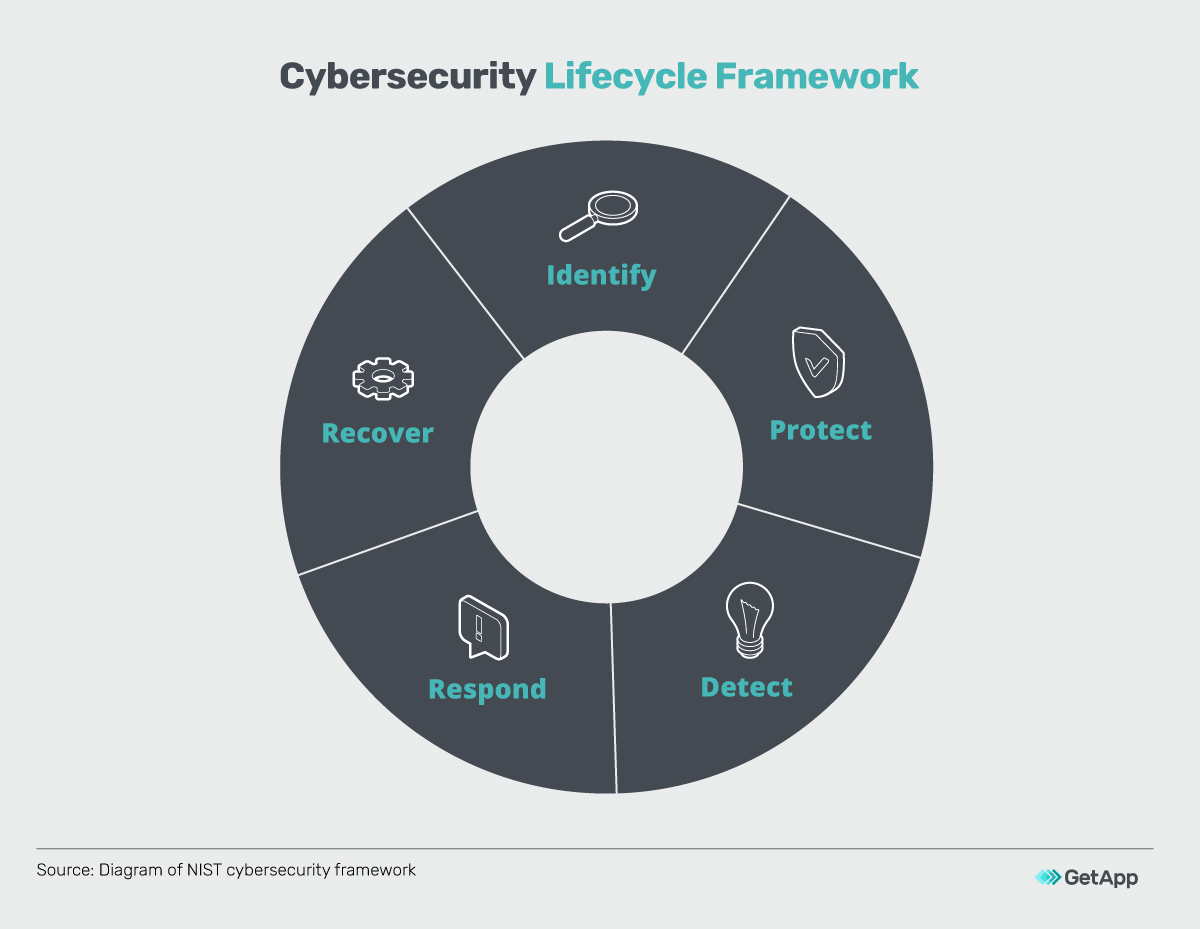
1. Identify: Assess the security risk
To protect your business from cyber criminals you need to first identify the valuable cyber assets and information that can be prime targets. You’ll need to inventory your assets and implement data classification policies, which will help you assess the kind of threats your business faces.
This initial research is also crucial to prioritizing security investments for the IT assets that can have the biggest business impact in the event of a cyber attack.
Further, with a clear understanding of the different kinds of cyber risks your IT assets carry, you can formulate suitable security policies to prevent the inappropriate use of your IT assets.
Track and organize users’ access to data: Data classification is the process of categorizing data to identify the critical information that needs to be protected from hackers. You can categorize data classification levels as public, private, and restricted based on the sensitivity of a piece of information.
You can then create a data classification policy to control and track the varying degrees of access different users have to your data.
Inventory your IT assets: This involves tracking hardware and software assets and determining their vulnerabilities. While you can use a spreadsheet to do this, an easier and faster way is to use IT asset management software.
Such a tool will help you map different IT assets, from SaaS applications to IoT devices, and automatically track systems that need upgrade or replacement.
Learn more
Click here to learn more about the benefits of using IT asset management solutions.
2. Protect: Implement security measures
Once you’ve identified the valuable cyber assets and information you’re looking to protect, it’s time to adopt security measures. Protecting your businesses is a multi-pronged approach and by combining the right mix of security solutions and employee training, you can ensure that your business data and IT assets receive layered protection.
While cybersecurity software solutions will keep your networks, systems, and data from being hacked, security training ensures that your employees are aware of the potential threats and diligent about their workplace behavior.
Use the right cybersecurity solutions: The initial risk assessment will allow you to build a prioritized list of the threats you want to protect your business from. The cybersecurity solutions you’ll procure will be based on this list.
Cybersecurity solutions are designed to protect different elements of your IT ecosystem. Broadly, these elements and their related security solutions can be classified into three segments: network security (tools include VPNs for remote working and application firewalls to prevent phishing attacks), system security (tools include antivirus software to prevent malware downloads and patch management software to ensure systems are updated with the latest configurations), and data security (tools include encryption software that adds cipher sensitive information housed in websites, databases, folders, etc.)
Conduct security training: One of the biggest cyber risks that are often overlooked is insider threats. Employees can inadvertently download malware when using productivity tools on the web. Likewise, they can be tricked into clicking malicious links on emails.
To prevent well-meaning but ill-informed employees from falling prey to cyber crime, you must train them on security best practices such as password management and identifying phishing attacks. You also need to regularly update the training program on new threats and send employees reminders to complete the training.
Learn more
3. Detect: Monitor threats proactively
Proactive threat detection is a critical phase in the cybersecurity lifecycle framework as it enables your business to prevent hackers from entering into your systems and staying undetected, which can sometimes be up to four years.
This requires you to continuously monitor the logs on your networks, devices, and applications for detecting any incidents or threats. It also involves conducting security assessments to identify vulnerabilities and fix them before they turn into serious cybersecurity events.
By having an active threat monitoring process in place your business will be better able to respond to and recover from cyber attacks.
Create a data logging policy: The first step to ensure proactive threat monitoring is determining which systems’ logs need to be monitored and the kind of log settings to be enabled. The trick to log management is to find the right balance between insufficient logging (which may compromise the security of your systems/networks) and extreme logging (which may lower system performance).
A data logging policy helps create that balance by allowing cybersecurity professionals to spell out the exact details of log management—what needs to be logged and when, how the logs will be stored, how frequently they will be reviewed, etc.
Perform security testing: Security testing such as a penetration test can help in detecting the kinds of threats your networks and systems are likely to face. If you have security specialists (e.g. certified ethical hackers) in your organization, then you can conduct the test in-house using threat detection technologies.
You can also outsource security testing to a third-party such as a vulnerability assessment service company.
4. Respond: Create a response plan
No security framework is full-proof and persistent cyber attackers may find chinks in your security armor. To be prepared for any such event, you need an incident response plan.
Being ready with an incident response plan empowers your business to quickly come up with answers and solutions in case of any cyber attack. You’ll be able to correctly estimate its business impact, quickly notify the relevant stakeholders, and have a team ready to deal with the situation.
The ability to respond effectively and immediately can be the wall that stops a relatively minor threat from blowing into a data breach horror-tale.
Create a cyber incident response plan (CIRP): The CIRP document is a foundational resource that clearly defines what constitutes a cyber crisis for your business and outlines the remedial actions to follow. This crisis communication template can go a long way in timely communication with media, business partners, and clients.
To create this plan, you need to first form an incident response management team that consists of IT/security staff, human resources/legal staff, and volunteers. Further, you’ll need to chart out process workflows, such as the stakeholders and business partners to be notified in the wake of an attack.
Consider getting a cyber insurance policy: An extra insurance to cover cybercrime might sound like another capitalist trap. But when cybercrimes are costing companies $200,000 on average, annual cyber insurance premiums worth $1,000 to $3,000 for up to $1 million coverage are only logical.
Investments in cyber insurances are especially worthwhile for companies that deal with highly sensitive information such as medical records and banking details of clients. However, you need to thoroughly assess your business’s risk exposure (sensitivity of the data you store, industry regulations you need to follow, etc.) before purchasing insurance.
Learn more
5. Recover: Ensure business continuity
Without an effective business continuity plan, such as a data backup strategy, an organization can suffer tremendous financial losses. In our 2020 State of Data Security Report, we find that 75% of businesses paid ransoms to get their data back from hackers but 30% of them didn’t get their data back.
A business continuity plan makes your business more resilient to such events and is critical for the speedy restoration of your operations and IT systems. And the quicker you restore your operations and systems, the lesser resources you lose to disruption and the more your customers trust you with their data.
Establish a business continuity plan: A business continuity plan helps in bringing operations back to normal after a cyber attack. The first step to developing this plan is estimating the financial implications and operational and infrastructural damages of a potential cyber attack.
Thereafter, you’ll need to formulate strategies that aid recovery. An example is a data backup and recovery strategy that will help you keep copies of your data and reduce downtime in the wake of a data breach. Finally, you’ll need a team to quickly act and execute the business continuity strategies you have put in place.
Learn more
Cybersecurity investments could crash without a framework
There are numerous cybersecurity technologies on the market that you can use off-the-shelf to counter cyber attacks. But without a proper cybersecurity lifecycle framework, your cybersecurity investments could fail.
Think of it this way: cybersecurity investments are a vehicle intended to get your business to a certain point, a cybersecurity lifecycle framework is the wheel with which you make course-corrections, and you are the driver. Without the wheel, there is nothing much you can do about where your cybersecurity vehicle goes. And to keep the vehicle on the road, you’d need to make continuous adjustments to the wheel.
Additionally, if you’re a business just starting with cybersecurity then you need to take small steps toward implementing the framework as you’re likely to lack the IT expertise to achieve all the cybersecurity goals at once.
Note
This report chooses the NIST framework as it’s a popular set of guidelines for creating cybersecurity programs and is suitable for businesses of any size. There are several other security standards and frameworks, such as the ISO/IEC 27001, and it’s recommended that every business evaluates these frameworks to ensure using one that suits their unique security requirements.

Pritam Tamang