
GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
Ransomware Statistics, Trends, and Tips You Need to Protect Your Business
Ransomware is on the rampage, impacting everything from hospitals to entire cities. Read on to learn about the ransomware statistics, trends, and tips you need to know to keep your business safe.

NOTE: This article is intended to inform our readers about business-related concerns in the United States. It is in no way intended to provide legal advice or to endorse a specific course of action. For advice on your specific situation, consult your legal counsel.
Throughout this piece, we’ll analyze ransomware statistics from our recent data security survey (methodology at bottom of the page), catch you up on the latest ransomware trends, and share tips to protect your business as we look toward 2021.
Ransomware allows hackers to hold your data hostage
Ransomware is a type of malicious software that encrypts data and blocks access until a payment is made, typically in the form of cryptocurrency. Modern ransomware encryption uses randomly generated asymmetric and symmetric keys, the latter of which the attacker provides upon payment (the ransom) so that the victim can decrypt their files.
Ransomware statistics you need to know
To help you better understand the impact ransomware attacks are having on businesses like yours, we recently surveyed employees at 868 organizations. Our research found that 28% of businesses have been hit by a ransomware attack in the last 12 months.
What percentage of ransomware victims pay the ransom?
Whether or not to pay the ransom is the biggest choice victims face during an attack. Our research found that three out of four (75%) ransomware victims chose to pay the ransom.Many organizations choose to pay the ransom because it can reduce costly downtime and recovery costs. Just ask the city of Baltimore, which refused to pay a $75,000 ransom during a 2019 attack that took out city services for weeks. After all was said and done, Baltimore’s refusal to give in to the ransom demand cost the city more than $18 million in new hardware, lost revenue, and other recovery expenses.
What percentage of ransomware victims get their data back?
We found that 70% of businesses that paid the ransom regained access to their data. It makes sense that ransomware payments pay off more often than not, because it’s in the best interest of operators to reciprocate. Otherwise, the entire scheme falls apart and nobody would pay going forward.
That said, there are many reasons why you shouldn’t pay the ransom. Despite the high ransom payment success rate, it also means 30% of businesses that paid lost both their data and their money. Moreover, payments make the scheme more successful, thus encouraging more attacks against others and potential repeat attacks against your own company.
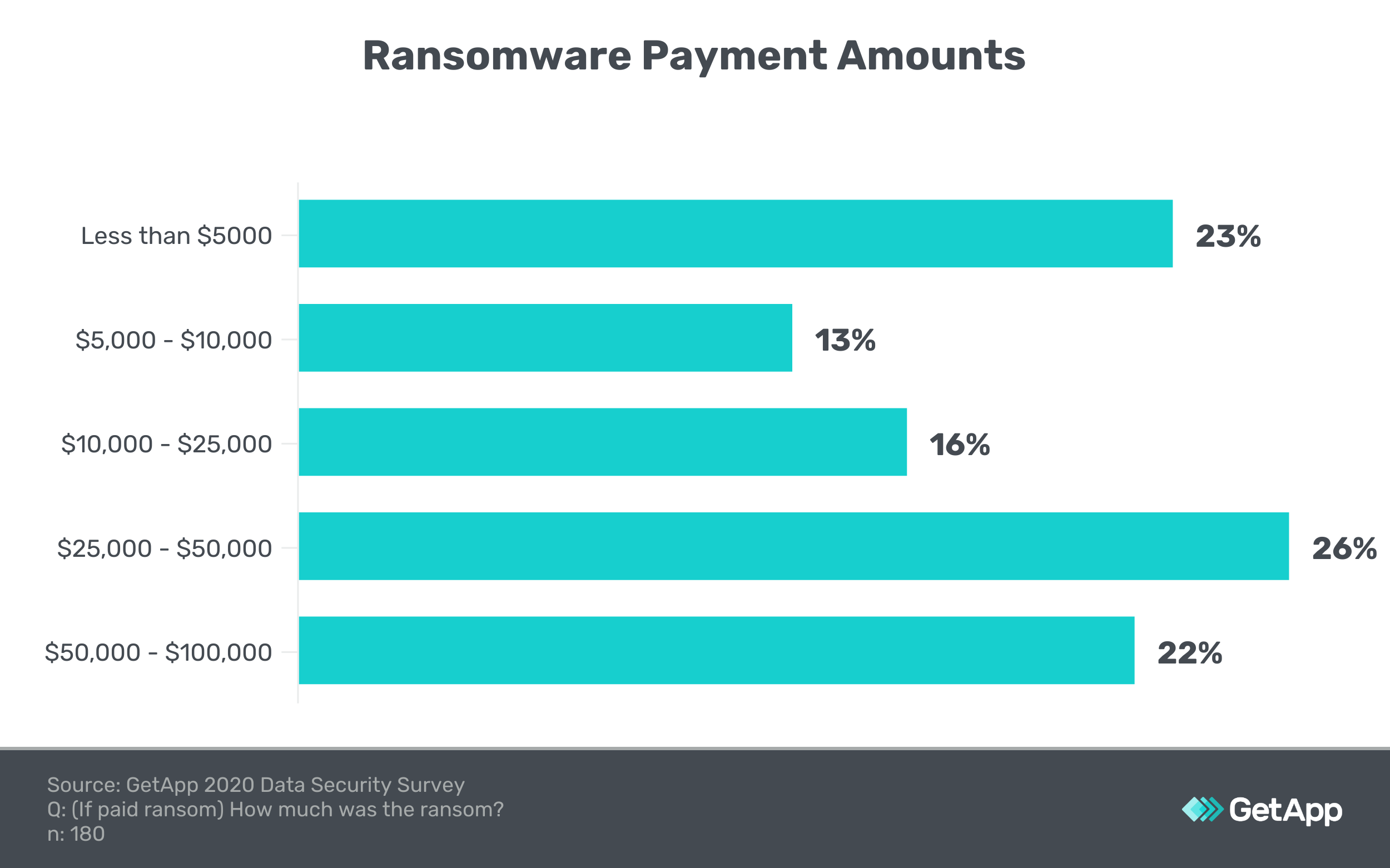
What is the average ransomware payout?
Our research found that nearly half (48%) of all ransomware payments were more than $25,000. More than one out of five payments exceeded $50,000. Only one survey respondent indicated a ransom demand above $100,000.
Backing up your data is the single most important step you can take to prevent the nightmare scenario of a total data loss. We recommend protecting yourself with data backup software in case the ransom payment doesn't work out or you’re unable to decrypt the data via other means.
Since ransomware can infect your live incremental backups as well, it’s also critical to make full system backups on a regular basis and store them separately from the rest of your network.
How does ransomware attack your network?
Ransomware can enter your network through remote ports, insecure servers, or even vulnerable internet of things (IoT) devices. Weaknesses in software—especially as-yet-unknown vulnerabilities called zero day exploits—are another common entry point.
Newer ransomware variants such as NotPetya harvest network credentials from temporary memory and escalate data access privileges to gain wider network access. This strategy aligns with our findings that ransomware attacks are far more common at organizations with lax data access policies. Sixty percent of businesses that allow employees full access to all company data suffered a ransomware attack, compared to only 10% of businesses that limit data access to what employees need to perform their job.
Despite ransomware’s increasing sophistication, ordinary email phishing remains a primary cyberattack vector for infections. In fact, Sodinokibi (currently the top ransomware threat) spreads primarily through bogus email attachments.
When we asked workers if anyone in their organization had clicked on a malicious link in a phishing email, 91% of those at companies that had experienced a ransomware attack said yes, compared to only 45% at companies that didn’t report a ransomware attack. In other words, employees at companies with ransomware attacks were twice as likely to have clicked a malicious link in a phishing email.
We also found that only 38% of companies that experienced a ransomware attack use email security software, compared to 62% of companies that weren’t attacked. To mitigate the threat of all types of malware, businesses must prioritize email security and train employees to recognize phishing schemes.
The history and evolution of ransomware
Ransomware debuted back in 1989 when a malware strain known as “AIDS” was sent to attendees of that year’s International AIDS Conference on infected floppy discs titled “AIDS information”. After infecting machines, the virus instructed victims to mail $178 to an address in Panama to regain access to their files.
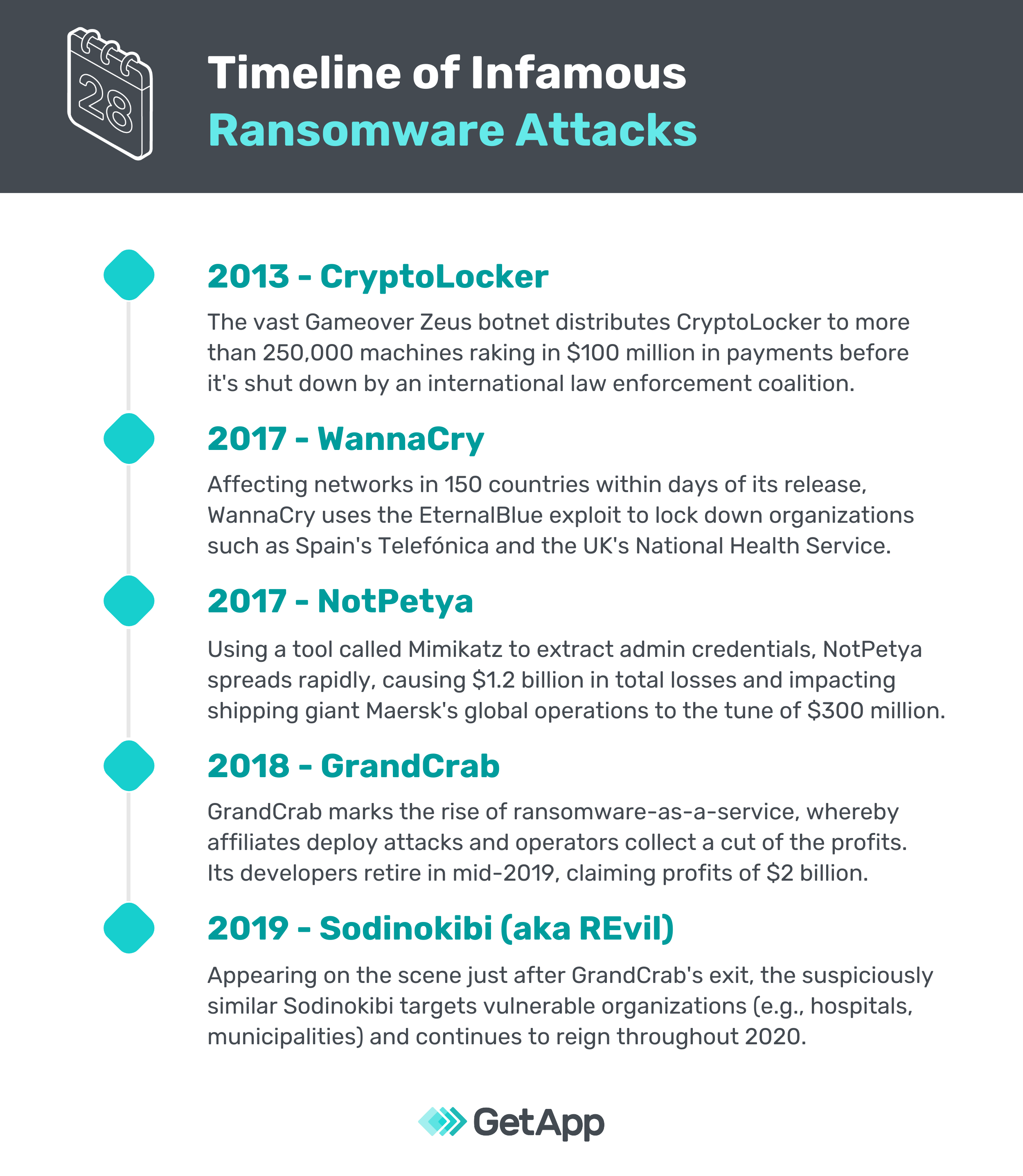
But it wasn’t until 2013 and the rise of CryptoLocker that modern ransomware strategies emerged. Cryptocurrencies such as Bitcoin supercharged ransomware, allowing attackers to obtain payments anonymously while more advanced asymmetric encryption methods streamlined the scheme.
Ransomware finally became a household term in April 2017 when WannaCry burst onto the scene, spreading across 150 countries and infecting more that 100,000 machines in only a few days. Take a look at this timeline of infamous ransomware attacks, from CryptoLocker to the latest and greatest threat, Sodinokibi (aka REvil):
Recent ransomware trends indicate growing risks to your business
Increasing use of ransomware-as-a-service
Recent years have seen the democratization of ransomware. The gangs behind GrandCrab, Sodinokibi, and Maze operate ransomware-as-a-service (RaaS) whereby affiliates are approved to launch attacks if they give the operator a cut of the profits.
Showing further sophistication and organization, these groups continually update their code and use obfuscation techniques to evade detection by the most advanced security tools. This allows cybercriminals to aim ransomware schemes at bigger and more complex targets for maximum payouts.
Exploiting IT outsourcing services
Ransomware attackers are compounding their schemes by aiming at managed service providers (MSPs), which handle IT services for an array of clients. That means ransomware operators might only need to gain access to a single MSP’s network to gain access to all of its customers.
A recent ransomware attack on one MSP led to the shutdown of 22 Texas cities, while another disabled over 400 dental practices in Wisconsin. MSPs are often breached via poorly secured remote access tools, such as remote desktop protocol (RDP). In the age of remote work, your business must take these vulnerabilities into account.
Spreading to mobile devices
Mobile ransomware attacks are on the rise, proving such schemes can be effective on any device (including iPhones). Spreading through sketchy websites and unofficial apps, mobile ransomware takes advantage of lax permissions, emergency alerts, and other mobile device features.
Rather than encrypt phone data, most mobile ransomware variants (such as the ubiquitous MalLocker) simply cover every app or browser window with a ransom note, rendering the device virtually unusable. This is how many strains of standard ransomware worked only 10 years ago, so you can bet cryptoviral mobile ransomware is just around the corner.
For now, users can attempt to uninstall mobile malware by restarting their device in safe mode or conducting a factory reset.
Upping the pressure
Ransomware gangs are innovating to make their schemes more severe. Take wiper malware for example, which some groups are incorporating with their ransomware viruses. This means that if you don’t pay, your encrypted files will be wiped out and impossible to recover. Some ransomware groups are incorporating DDoS attacks into their bag of tricks, making a victim’s customer-facing website inaccessible while waiting for a ransom payment.
Ransomware variants such as Maze are also dabbling in blackmail by exfiltrating a victim’s data prior to encryption and threatening to release sensitive data on the internet if payment isn’t made. This all means that not only is ransomware a cybersecurity risk, it’s evolving into a data breach risk that carries additional ramifications such as regulatory fines and reputational harm.
Targeting the most vulnerable
Another worrying trend is the targeting of vulnerable organizations such as healthcare organizations, universities, and municipalities. Atlanta, Knoxville, and Pensacola are among dozens of U.S. cities that have been attacked, while numerous hospitals across the country have experienced network outages. Cybercriminals have also taken full advantage of the COVID-19 pandemic, even attacking vaccine research firms.
In October 2020, Microsoft disrupted the Trickbot botnet (a known ransomware distributor) to prevent impacts on computer systems used to maintain voter rolls and tabulate election results. The same week, G7 leaders sounded the alarm about the growing ransomware threat to the critical infrastructure of countries around the world. Two weeks later, the U.S. Cybersecurity & Infrastructure Security Agency (CISA) issued an alert warning of widespread attacks on healthcare organizations, primarily by Ryuk ransomware using Trickbot and Emotet trojans.
Clearly, ransomware risks are growing in both variety and severity.
Tips to mitigate ransomware threats to your business
These ransomware statistics and trends can help you better understand how your peers are reacting to the tough decisions that come with an attack. But every business is different, and so is every ransomware incident.
What makes sense for another company might not for your business. But every organization can mitigate ransomware attacks by following these tips:
Conduct a risk assessment to gauge your current security posture.
Continuously back up data and develop a recovery plan in case of an attack.
Implement a data classification system and restrict data access privileges.
Practice network segmentation so that access to one part of your network doesn’t allow access to all of it.
Adopt antivirus software that includes fileless malware and ransomware detection.
Use endpoint protection software to monitor and protect network-connected devices.
Use strong passwords and enable two-factor authentication whenever possible.
Enable automatic updates on all operating systems and software applications.
Deploy email security software and educate employees about social engineering and advanced phishing techniques.
Secure mobile devices with endpoint protection software and by restricting phone settings and permissions.
Ensure remote workers are accessing your network securely.
If you do find yourself to be a ransomware victim and are considering paying the ransom, first contact your local FBI field office and report the attack to the Internet Crime Complaint (IC3). Consider arranging a trial key to ensure your data can actually be decrypted. If the attackers are not responsive, you should probably think twice before paying the ransom.
If payment is requested via cryptocurrency (e.g., Bitcoin, Monero), you will need to create an account with a reputable exchange to purchase the relevant coins and transfer them to the attacker. This is not a simple process; establishing a new account typically takes several days. For these reasons, it may be in your best interest to learn a bit about cryptocurrencies and establish an account so you’re not caught off guard if the time comes that you need it.
If you choose not to pay, you can attempt to resolve the malware yourself using ID Ransomware to identify the ransomware strain you’re dealing with. You can then try various known decryption keys available from nonprofits such as the No More Ransomware project. It's worth noting that 16% of the ransomware victims in our survey were able to remove the malware or decrypt their system without paying the ransom.
Looking for solutions to protect your business against cybersecurity threats?
Visit our IT security software catalog
Methodology
GetApp’s 2020 Data Security Survey was conducted from September 10 to September 11 among 868 respondents who reported full-time employment in the United States.


