GetApp offers objective, independent research and verified user reviews. We may earn a referral fee when you visit a vendor through our links.
Our commitment
Independent research methodology
Our researchers use a mix of verified reviews, independent research, and objective methodologies to bring you selection and ranking information you can trust. While we may earn a referral fee when you visit a provider through our links or speak to an advisor, this has no influence on our research or methodology.
Verified user reviews
GetApp maintains a proprietary database of millions of in-depth, verified user reviews across thousands of products in hundreds of software categories. Our data scientists apply advanced modeling techniques to identify key insights about products based on those reviews. We may also share aggregated ratings and select excerpts from those reviews throughout our site.
Our human moderators verify that reviewers are real people and that reviews are authentic. They use leading tech to analyze text quality and to detect plagiarism and generative AI.
How GetApp ensures transparency
GetApp lists all providers across its website—not just those that pay us—so that users can make informed purchase decisions. GetApp is free for users. Software providers pay us for sponsored profiles to receive web traffic and sales opportunities. Sponsored profiles include a link-out icon that takes users to the provider’s website.
How to Send Documents Securely Over the Internet
Is your team sending sensitive documents securely over the internet? Keeping data secure while working remotely can be a challenge. Check out three types of software solutions built to protect business data from unauthorized access.

The demand for tools to keep data secure while collaborating across the internet has never been greater. In the U.S., large companies such as Facebook, Square, Box, and Slack have all extended work-from-home plans indefinitely due to COVID-19. My team won’t be back in the office until Fall 2021—at the earliest—which means we’ve all become pretty familiar with using VPNs on our work devices.
For those businesses that are just getting used to having remote employees, it’s a good idea to strengthen cybersecurity and protect sensitive documents that need to be shared online. With a wide range of IT security solutions on the market, it’s helpful to review specific software types along with the features that meet your business needs.
In this article, we’ll review three types of software designed to help your teams securely access and share data while using external or home networks. These solutions can proactively help businesses avoid costly cybersecurity mistakes. We’ll focus on file sharing, encryption, and VPN solutions and explore how each solution type can protect your business data from unauthorized access.
Solution #1: File sharing software
File sharing software offers collaboration tools that allow teams to share information quickly and securely. These solutions are designed to provide secure access to all stakeholders from any location and device with an internet connection.
Common features include document management, access controls/permissions, audit trails, messaging tools, and data encryption. Let’s look at two common features included in file-sharing software.
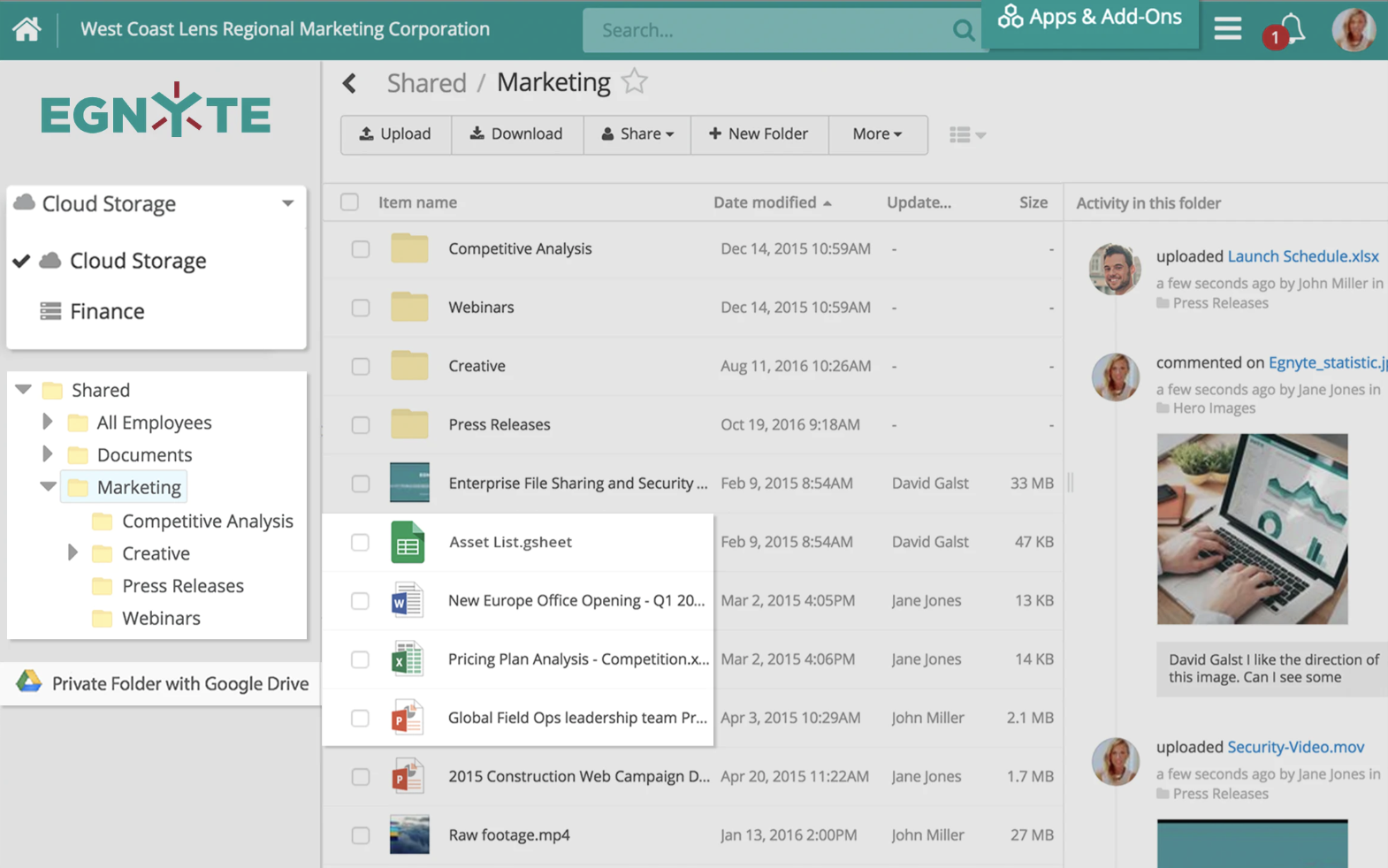
Use shared folder activity streams to monitor documents
With real-time activity streams for shared folders, businesses can ensure that teams are managing documents appropriately. By tracking any document changes and new uploads, this feature can help managers proactively identify any suspicious activity, such as an unauthorized user making unexpected document changes or sharing files with others.
The activity stream shown in the screenshot below tracks what document changes were made, who made them, and when. This feature is beneficial for managers who lead a large team of employees that must share sensitive documents during project collaboration.
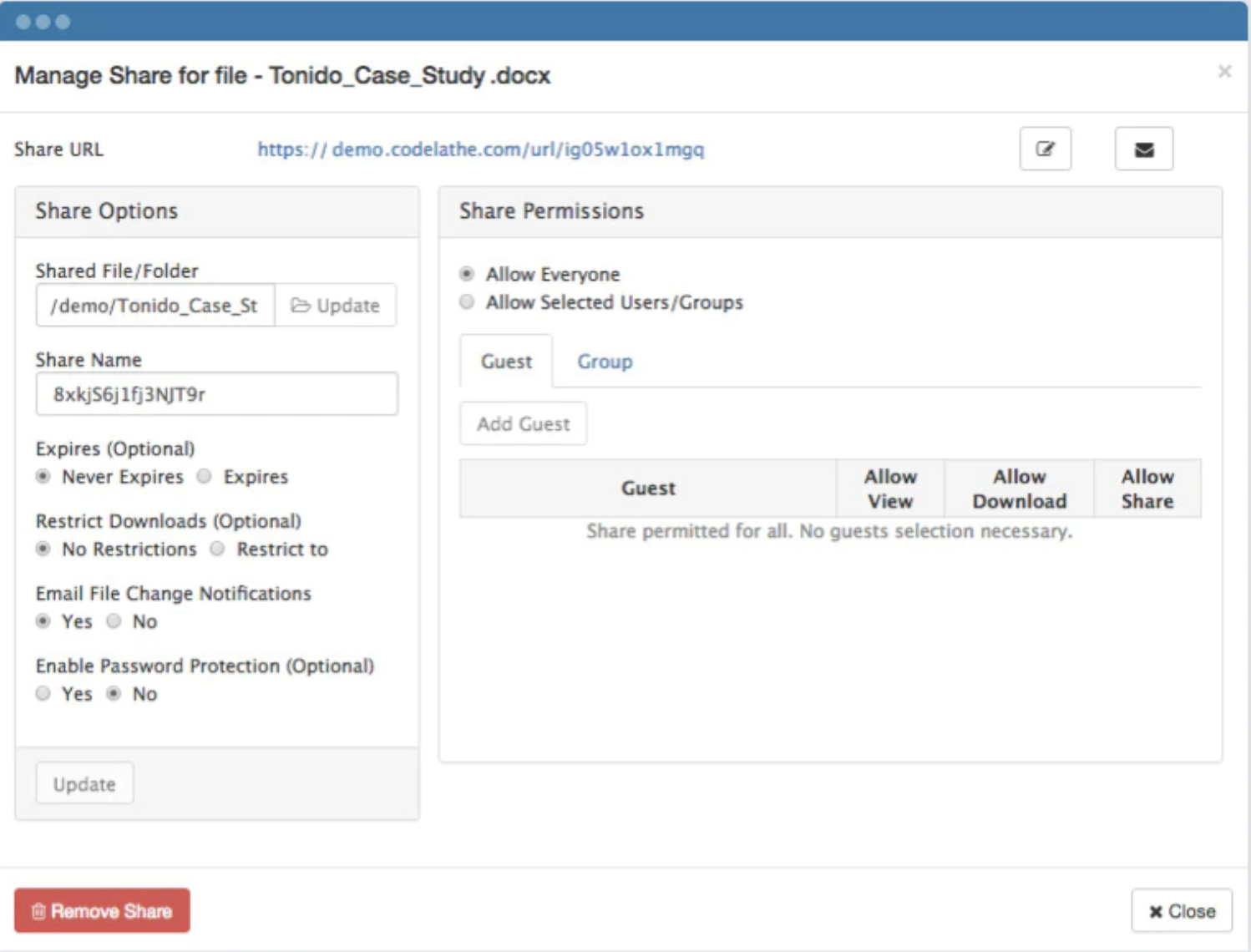
Manage document access with custom sharing options
It's common for file sharing solutions to provide sharing options such as customizable folder permissions, download restrictions, and access expiration dates. The screenshot below shows custom sharing and permission options that also include access expiration dates.
This sharing option can help businesses reduce the risk of unauthorized access by proactively limiting data accessibility to the right teams for specified amounts of time. For example, if a business partner needs access to a sensitive document for a one-week period to complete a research project, this feature allows document owners to set an expiration date for that file.
Read more
Check out our Category Leaders in File Sharing while narrowing down the best solutions for your business.
Solution #2: Encryption software
The second solution type we’ll look at is encryption software. Encryption solutions operate as security programs that prevent unauthorized access to content, files, networks, or applications. By encrypting, converting, or concealing data, these solutions can help your business protect sensitive data as it is shared across the internet with several teams.
Businesses that consistently share sensitive client information across the internet can benefit from encryption tools. Common features include compliance management, network monitoring, threat detection, password management, and secure data storage. Let’s look at a couple of helpful features.
Access cybersecurity tools that safeguard documents
Many encryption solutions include tools that monitor and protect data while it is being shared online using various applications, such as email and document readers. The screenshot below shows a network protection platform that includes various security tools, including network watch activity, threat and spam statistics, and malware cleaning.
With these types of tools, encryption solutions are designed to help businesses proactively prevent data breaches and block any targeted attacks.
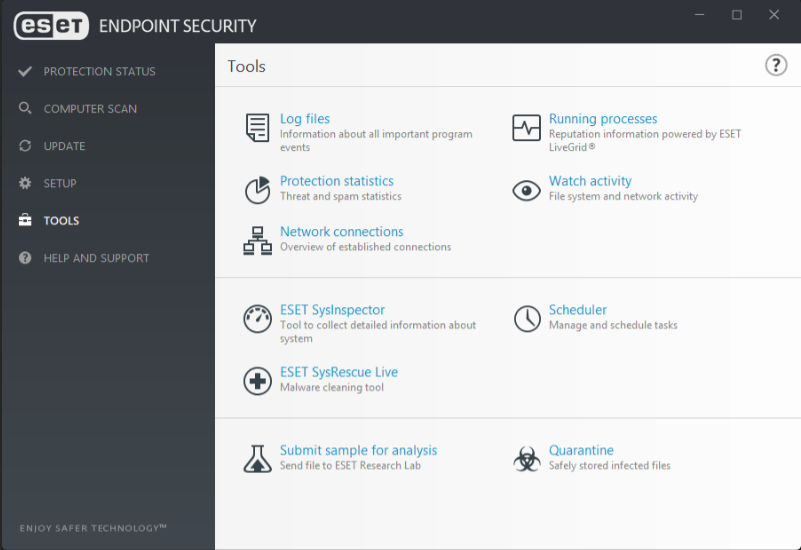
Built-in security tools on ESET Endpoint Security (Source)
Keep credentials secure with password protection
To further protect sensitive data, encryption software may include features that protect credentials, including client passwords. With employees working remotely and using various networks and applications to communicate with other teams, partners, and clients, password protection is crucial.
The screenshot below shows various credential protection options for password creation, routine password changes, and password resets. These options are suitable for managed service providers (MSPs) and IT teams that provide remote support to clients or other teams by temporarily accessing their devices. With these options, you can ensure passwords remain confidential and reduce cybersecurity risks as technicians access various types of information.
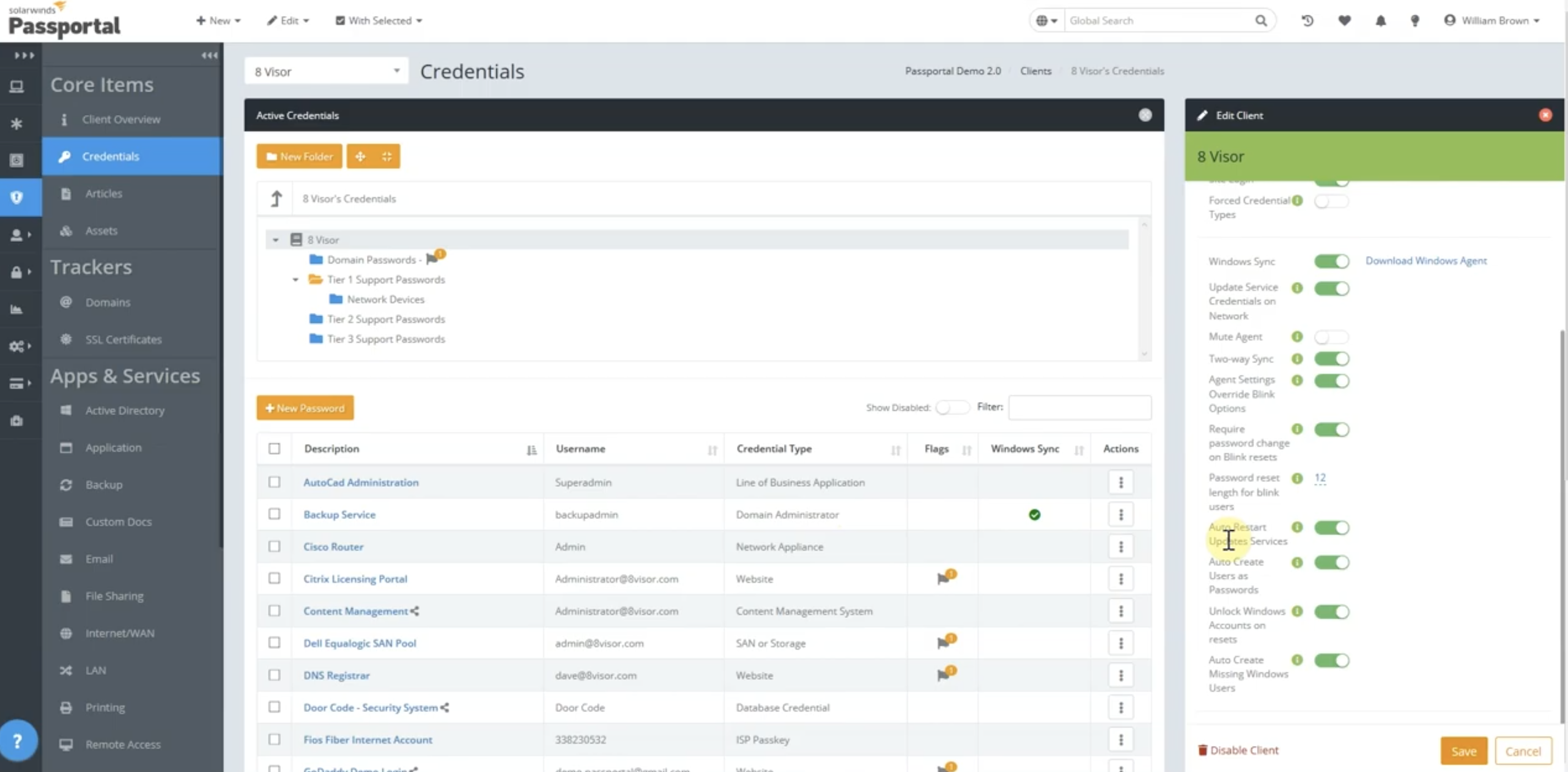
Credential and password management on SolarWinds Passportal (Source)
Solution #3: VPN software
The last solution type we’ll review is VPN, or virtual private network, software. These solutions allow remote teams to securely access corporate networks through encrypted connections.
VPN software is an effective way for businesses to protect data and safeguard shared documents. It establishes secure connections between employee devices and a web server, regardless of location. Common features include anonymous browsing, data encryption, DNS leak protection, and kill switch. Below, you’ll find two VPN features that are particularly helpful.
Reduce threats with secure network access
If employees access and send sensitive documents while working from home, public, or non-secure networks, business data is at risk. By implementing a VPN to connect to the internet, businesses can ensure that data is not vulnerable as it is being shared across the internet during team collaboration.
In addition to secure network access, VPN solutions often offer security analytics, threat protection, multi-factor authentication, extended roaming protection, plus other cybersecurity-focused tools. An example of a VPN solution can be seen in the screenshot below.
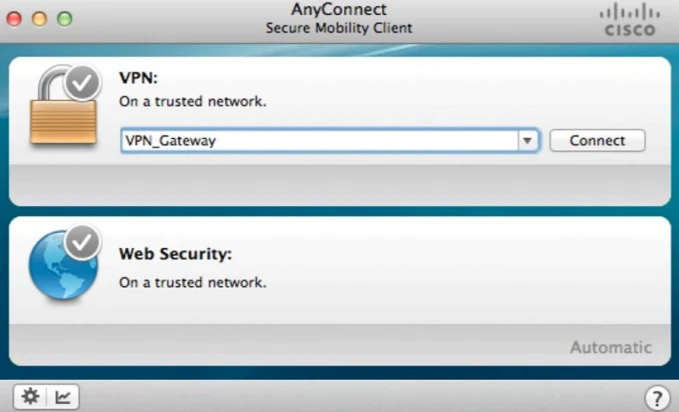
Secure enterprise network access using Cisco AnyConnect on a laptop (Source)
Use a kill switch to protect data during VPN drops
Some VPN software offers a kill switch feature. When VPN connections unexpectedly drop, the software’s kill switch can block internet traffic until a secure connection is restored.
This feature adds an extra layer of cybersecurity for employees who work on VPNs and must consistently send sensitive documents and information over the internet. Administrators can manage kill switch preferences, as shown in the screenshot below, to align with your specific business needs.
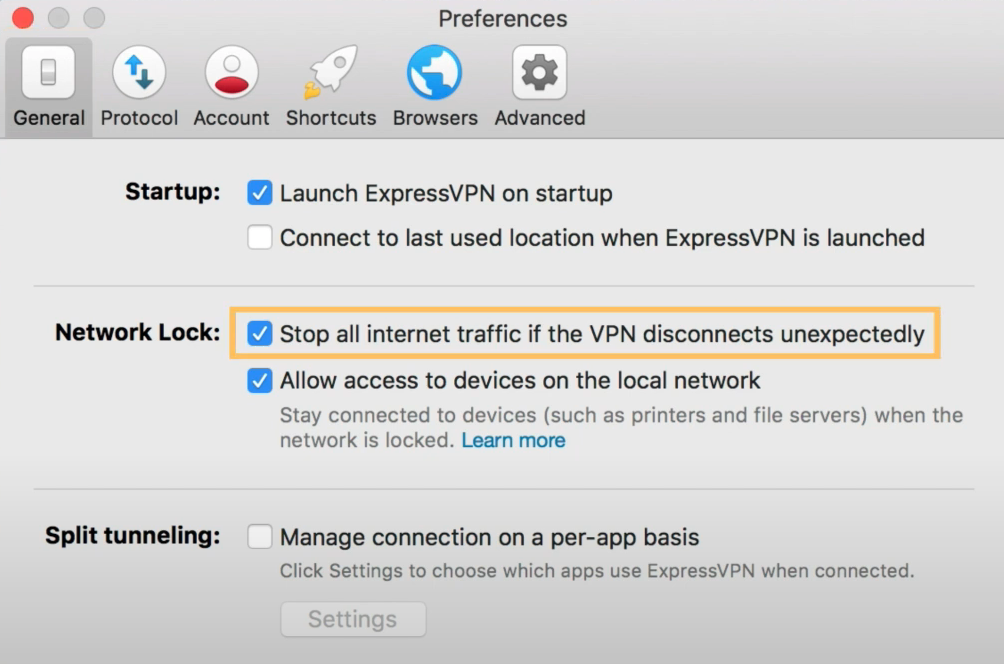
Preferences for ExpressVPN’s kill switch feature called Network Lock (Source)
Next steps for stronger cybersecurity
Remote work was on the rise even before the COVID-19 pandemic hit. However, this year, many businesses around the world—including ones that were not prepared to have a remote team—had to make big adjustments in a short period of time.
After our review, it’s clear that several types of software with various features exist to secure business data while employees share documents over the internet. To prevent unauthorized access or other cybersecurity threats, businesses should implement or continue to use software solutions that fit their own unique needs. Check out our catalogs for file sharing, encryption, and VPN solutions to choose a product for your team.
Note
The applications selected in this article are examples to show File Sharing, Encryption, and VPN features in context and are not intended as endorsements or recommendations. They have been obtained from sources believed to be reliable at the time of publication.